Every attorney knows ABA Model Rule 1.6 by name.
Most could recite its core principle without hesitation: protect client confidentiality. What far fewer attorneys can articulate is what that obligation actually demands from the technology running their firm every single day.
That gap, between knowing the rule and understanding its technical implications, is where professional liability begins. A shared cloud environment where client files commingle with other organizations’ data. Remote access configured without multi-factor authentication.
A practice management platform hosted on infrastructure that logs nothing and encrypts selectively. None of these feel like Rule 1.6 violations during setup. Each of them can become one.
This article breaks down what IT support for law firms must actually deliver under ABA Rule 1.6 in 2026, what those controls look like in practice, what happens when infrastructure falls short, and what a support relationship built around attorney-client confidentiality looks like from the start.
Table of Contents Show
Key Takeaways
- ABA Model Rule 1.6 requires attorneys to take “reasonable measures” to prevent unauthorized disclosure of client information, and in 2026, those measures are explicitly technology-dependent.
- In practice, reasonable measures means encryption, multi-factor authentication, access controls, and audit logging are baseline requirements, not optional features.
- Legal practice management software including Clio, MyCase, PracticePanther, Smokeball, and CosmoLex must be hosted in secure, dedicated environments to satisfy the rule’s confidentiality requirements.
- Technology failures, including data breaches, inadequate access controls, and improperly secured cloud environments, can trigger bar discipline, malpractice claims, and court sanctions.
- Technology support for law firms that is not aligned with ABA Rule 1.6 exposes the entire firm to professional liability that most general IT providers are not equipped to anticipate or prevent.
What ABA Model Rule 1.6 Actually Says
ABA Model Rule 1.6 is the foundational confidentiality rule under the ABA Model Rules of Professional Conduct.
Its core obligation is straightforward: attorneys must not reveal information relating to the representation of a client without informed consent. But the rule does not simply define what attorneys cannot say. It also creates an affirmative duty to take steps that prevent unauthorized disclosure from occurring in the first place.
That duty to act is where technology enters the picture. ABA Formal Opinion 477R (2017) and ABA Formal Opinion 498 (2021) have each clarified that the rule’s confidentiality requirements extend to cloud computing, electronic communication, remote access, and the full range of digital tools that define modern legal practice.
ABA Formal Opinion 483 (2018) extended that obligation further, establishing that attorneys have an affirmative duty to monitor their systems for breaches and to act promptly to stop and remediate any breach once detected, making incident response a Rule 1.6 obligation, not just an operational best practice.
Selecting a cloud vendor, a practice management platform, or a managed IT provider is no longer a purely operational decision for a law firm. It is a compliance decision with professional conduct implications.
The “Reasonable Measures” Standard
The specific language Rule 1.6 uses is “reasonable measures.” The rule requires attorneys to “make reasonable efforts to prevent the inadvertent or unauthorized disclosure of, or unauthorized access to, information relating to the representation of a client.”
Reasonable is not a fixed technical specification. It is a contextual standard that weighs the sensitivity of the information, the probability of unauthorized access, and the cost and feasibility of implementing protective safeguards.
A solo practitioner handling routine real estate transactions operates in a different risk environment than a mid-sized litigation firm managing privileged communications in high-stakes corporate disputes.
But for any law firm operating with cloud-based software, networked devices, or remote access in 2026, the controls that meet the reasonable measures threshold are substantive. AES-256 encryption of all data at rest and in transit, multi-factor authentication on every login, role-based access controls that govern who can see what, and comprehensive audit logging of all access events are the baseline.
These are not enterprise luxuries reserved for large firms with dedicated security teams. They are what “reasonable” actually looks like for any practice environment handling privileged attorney-client communications.
How ABA Rule 1.6 Differs From IRS Publication 4557
Law firms occasionally encounter IRS Publication 4557 in conversations about data security, particularly when evaluating technology providers who also serve accounting practices. Understanding the difference between these two frameworks matters before signing any technology contract.
ABA Model Rule 1.6 governs attorney-client confidentiality and is enforced through state bar associations under professional conduct rules. It applies to any attorney subject to the ABA Model Rules.
IRS Publication 4557 is federal regulatory guidance that governs data security specifically for tax preparers, enforced by the IRS, and requires a Written Information Security Plan (WISP). A law firm that does not provide tax preparation services is not subject to IRS Publication 4557.
Both frameworks require similar technical safeguards, including encryption, access controls, and incident response planning, but the compliance obligations, enforcement mechanisms, and liable parties are entirely different.
A managed IT provider serving both law firms and accounting practices must understand which regulatory framework applies to which client and structure its approach accordingly. Conflating the two frameworks is not just a compliance error. It signals that the provider has not done this before.
What Law Firm IT Support Must Cover to Meet ABA Rule 1.6
The “reasonable measures” language in Rule 1.6 is deliberately flexible, but it is not vague. When applied to a law firm’s actual technology environment, the controls it points toward are specific, verifiable, and increasingly standard in any professional services context that handles sensitive client data.
Any managed technology services provider working with a law firm should be able to address each of the following in concrete, documented terms. A provider that cannot is not equipped to serve a practice operating under attorney-client confidentiality obligations, regardless of how its services are marketed.
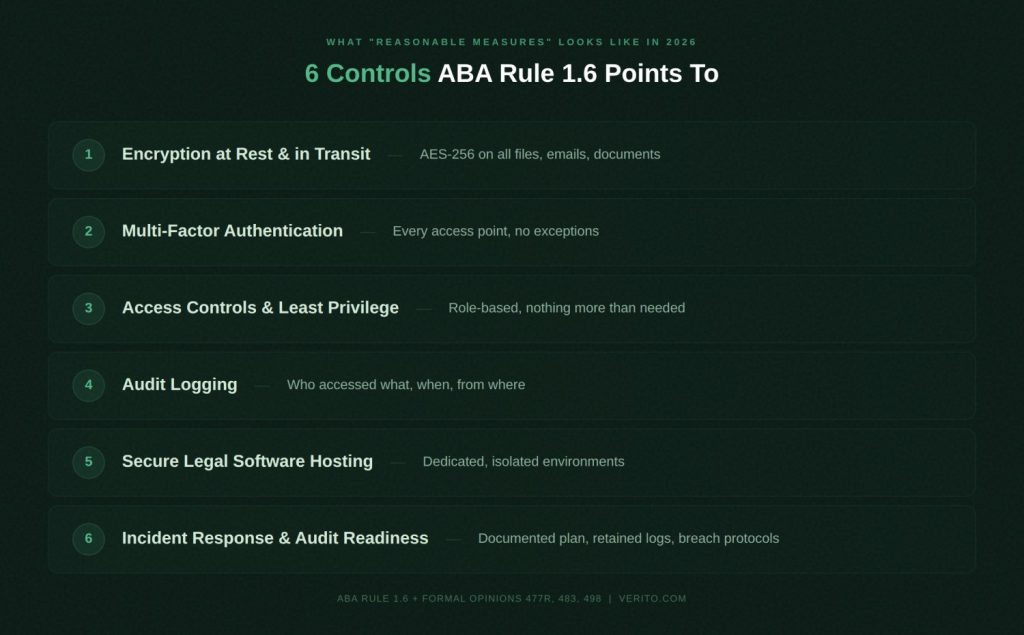
1. Encryption at Rest and in Transit
Every client communication, case file, legal document, and piece of correspondence must be encrypted both when stored and when transmitted across any network. AES-256 encryption is the current industry standard for both states. This applies to email, cloud-stored documents, file transfers between attorneys and clients, and any data passing through remote access connections.
A firm whose infrastructure relies on unencrypted storage, or that transmits client data over unprotected channels, is not meeting the reasonable measures standard, regardless of how its technology has been priced or packaged. Encryption is not a feature tier. It is the architectural foundation on which everything else depends.
2. Multi-Factor Authentication on All Firm Systems
Multi-factor authentication (MFA) is the single control that prevents a stolen credential from becoming a full breach. Without it, a single compromised password obtained through a phishing email, a credential-stuffing attack, or a careless account reset is sufficient to grant unauthorized access to every client file that account can reach.
MFA must be enforced across every access point: email platforms, practice management software, cloud environments, remote desktop connections, and any client-facing portals the firm operates.
The rule’s requirement to prevent unauthorized access to client information is practically impossible to satisfy in the current cybersecurity environment without it, and any technology partner who treats MFA as optional should be asked why.
3. Access Controls and Least-Privilege Architecture
Not every person in a law firm should be able to access every client matter. A billing administrator should not have visibility into privileged communications. A paralegal assigned to a contract dispute should not be able to open criminal defense files. A support staff member with no case responsibility should not have file-level access to active litigation materials.
Least-privilege architecture means each user accesses only what their role specifically requires, and nothing beyond that. This approach limits the attack surface significantly.
If a staff account is compromised, the scope of potential exposure is bounded by that account’s defined access level. It also creates an internal control structure that addresses human error and intentional misuse with the same mechanism.
4. Audit Logging
Audit logging is the record of who accessed which files, at what time, and from which device. For law firms operating under confidentiality obligations, these logs serve two distinct functions:
- The first is deterrence: people behave differently when they know their actions are recorded.
- The second is evidentiary: in the event of a breach investigation, a bar complaint, or a malpractice proceeding, audit logs are often the primary evidence of what actually happened and whether adequate controls existed before the incident.
ABA Formal Opinion 483 treats the absence of this logging infrastructure as a contributing factor to an ethical violation, not merely an operational shortcoming. A firm that cannot produce that record is entirely at the mercy of assumptions.
5. Secure Legal Software Hosting
Practice management platforms are the operational core of a modern law firm. Clio, MyCase, PracticePanther, Smokeball, and CosmoLex each handle case data, client communications, billing records, and document storage that fall squarely within the scope of attorney-client confidentiality. Where and how these applications are hosted has direct compliance implications.
Hosting these platforms on shared cloud infrastructure, where a law firm’s data resides on the same physical or logical server as unrelated organizations, introduces cross-contamination risk that a dedicated, isolated environment eliminates.
Document management platforms like NetDocuments and iManage carry the same requirement. The security posture of the hosting environment must match the sensitivity of what runs on it. Shared infrastructure is not a neutral choice. It is a risky decision.
6. Incident Response and Audit Readiness
ABA Rule 1.6 compliance is not a one-time certification that a firm achieves and maintains passively. It is an ongoing operational posture that includes being prepared for when something goes wrong.
A documented incident response plan defines who is notified when a breach occurs, what steps are taken to contain the damage, how affected clients are informed, and what evidence is preserved for regulatory and legal purposes.
The technology infrastructure a firm uses must support this process rather than create obstacles to it. That means retained audit log data with clearly defined retention periods, documented access hierarchies, and a support relationship with a provider capable of responding to security incidents quickly and with legal context intact.
Law Firm Data Security Failures: What ABA Rule 1.6 Violations Actually Cost
Understanding the technical requirements creates clarity. Understanding the consequences of falling short creates urgency.
Technology-related confidentiality failures are not edge cases confined to large firms with high-value targets. According to the ABA’s 2023 Legal Technology Survey Report, 29% of law firms reported that their firm had experienced a security breach at some point.
For small and mid-sized practices, where dedicated IT resources are thinnest and reliance on off-the-shelf technology is highest, the exposure is consistent and real. The question most managing partners face is not whether a breach could happen, but whether their current infrastructure would contain the damage if it did.

1. Bar Discipline and License Risk
A technology failure that results in the unauthorized disclosure of client information can form the basis of a bar complaint and formal disciplinary proceedings.
State disciplinary authorities have become increasingly sophisticated about evaluating whether a firm had implemented adequate safeguards before a breach occurred. The question they ask is not just what happened. It is whether the firm had taken the reasonable measures Rule 1.6 requires.
Attorneys found to have violated the rule through inadequate technology controls face outcomes ranging from public censure to license suspension. In cases involving severe or repeated failures, disbarment is a documented outcome. The professional consequences attach not just to the firm entity but to individual attorneys within it, making every partner personally exposed to the technology decisions the firm makes collectively.
2. Malpractice Claims and Court Sanctions
The liability exposure does not stop at the bar. Clients whose confidential information is disclosed as a result of a technology failure may have grounds for a civil malpractice claim, particularly where they can demonstrate that the disclosure caused concrete harm. In litigation contexts, a breach affecting privileged communications or discovery materials can also invite court-imposed sanctions.
The financial exposure is not limited to direct legal liability. The IBM 2024 Cost of a Data Breach Report found that the global average cost of a data breach reached $4.88 million, a figure that includes legal fees, regulatory penalties, notification costs, and operational disruption. For a small or mid-sized law firm operating on the margins of that exposure, even a fraction of that figure can be firm-ending.
3. Reputational Damage
The reputational consequences of a breach often materialize faster and hit harder than the legal consequences. Clients who trusted a firm with sensitive matters, family law proceedings, criminal defense, corporate transactions, personal injury claims, do not remain clients after learning their information was exposed. They leave quickly, and the information travels through referral networks that took years to build.
Law firm relationships are built on a level of trust that few other professional service relationships reach. The barrier to entry for a new client is high precisely because the barrier to exit after a breach is nearly zero. No marketing effort closes that gap once it has opened.
How Verito’s Infrastructure Satisfies ABA Rule 1.6 for Law Firms
Verito is a cloud hosting and managed IT provider built for compliance-driven professional services firms. Its IT support built for law firms is designed around the specific confidentiality and uptime requirements of legal practice, not adapted from a generic infrastructure product.
For law firms, that means the technical controls ABA Rule 1.6 expects are present at the baseline of every plan. Verito’s cloud infrastructure includes AES-256 encryption at rest and in transit, MFA on every login, and audit logging, all aligned with ABA Model Rule 1.6 requirements for attorney-client data confidentiality.
Dedicated-Isolation Architecture
Every law firm using Verito operates in a completely isolated environment. The Dedicated-Isolation Architecture™ means no shared resources, no shared infrastructure, and no shared risk with any other organization’s data or network activity.
Each client environment is provisioned as a dedicated private server instance with dedicated vCPUs, dedicated RAM, and isolated storage.
This eliminates the cross-contamination risk that shared cloud environments create for attorney-client confidentiality. Firm data does not commingle with any other organization’s data at any layer of the stack, which is the architectural approach the reasonable measures standard points toward for any firm handling sensitive privileged communications in a cloud environment.
24/7 VeritCertified Support for Legal Workflows
Every Verito engineer passes VeritCertified training before working with clients. For law firm clients, that training includes working knowledge of legal practice management platforms: Clio, MyCase, PracticePanther, Smokeball, and CosmoLex.
When an issue arises, the support engineer understands how these applications work, what their failure modes look like, and how to resolve the problem without requiring an attorney to explain their own software to the person helping them.
The documented results from this model are specific. Verito maintains a sub-60-second average support response time, a 92% first-touch resolution rate, a 4.9/5 rating on G2 across 125 or more verified reviews, and a 100% uptime track record since 2016 across a client base of more than 1,000 firms. For a law firm in the middle of a filing deadline or pre-trial preparation, those are not background statistics. They are the operational foundation that makes professional deadlines survivable.
SOC 2 Type II Infrastructure and U.S.-Based Data Centers
Verito operates within Tier IV, U.S.-based data centers that hold SOC 2 Type II certification through Deft, the underlying infrastructure provider. SOC 2 Type II is an independently audited certification that verifies security, availability, and confidentiality controls have been consistently maintained over time, not just at a single point in time.
This certification level provides the third-party-verified evidence of security controls that an attorney would need to demonstrate reasonable measures in a bar inquiry, a cyber insurance audit, or a malpractice discovery proceeding.
Verito’s data center infrastructure includes built-in geographic failover, nightly automated backups, SSD-backed storage with triple redundancy, and a recovery architecture designed around the uptime demands of professional legal practice.
Choosing IT Support for Your Law Firm: Legal IT Compliance Questions to Ask Before You Sign
Most law firms arrive at this decision reactively, after an incident that made the stakes concrete, after a vendor relationship that worked until it stopped working, or after a bar association communication about data security obligations. Getting ahead of that moment requires asking specific questions before any contract is signed, not after the fact.
Not every provider that markets services to law firms understands legal compliance requirements. General managed services for small businesses are not the same as law firm technology management built around the specific demands of attorney-client confidentiality.
The difference between the two becomes visible in how providers answer the following questions. Providers equipped for legal practice answer them with specifics. Providers that are not, answer them with reassurances.
Questions to Ask Any IT Provider
Before committing to a technology partner, every managing partner or firm administrator should get clear, documented answers to these:
- Do you have direct experience hosting legal practice management software, including Clio, MyCase, PracticePanther, Smokeball, or CosmoLex?
- Is each client’s environment fully isolated from other clients, or is firm data on shared infrastructure with other organizations?
- Is AES-256 encryption at rest and in transit included as a standard on every plan, or is it a paid upgrade?
- Is multi-factor authentication enforced on every access point, including remote login and email?
- Do you maintain audit logs for all access events, and what is the documented retention period?
- How does your team respond when a security incident occurs, and what documentation do you provide the firm afterward?
- Are your data centers U.S.-based, and is your uptime SLA backed by a documented track record, or is it a contractual commitment without historical evidence?
For a broader view of what future-proofing your firm’s IT infrastructure means beyond the immediate compliance baseline, this resource on future-proofing your firm’s IT infrastructure covers the longer-term technology decisions worth evaluating at the same time.
ABA Rule 1.6 Compliance Has Always Required This. Your Technology Just Has to Catch Up
ABA Model Rule 1.6 has always required attorneys to take reasonable measures to protect client confidentiality. What has changed is the environment those measures must address. Cloud software, remote work, increasingly sophisticated phishing campaigns, and credential-based attacks have made “reasonable” in 2026 a substantive bar, not a minimal one.
Encryption, MFA, access controls, audit logging, and cybersecurity support for legal practices from a provider that genuinely understands attorney-client confidentiality obligations are not advanced features for large firms with dedicated compliance teams.
They are the baseline for any practice that handles privileged communications in a modern technology environment. A general IT provider without legal vertical experience can build technically sound infrastructure that still leaves compliance gaps a disciplinary authority or plaintiff’s counsel will identify clearly.
If you are not certain your current technology infrastructure would withstand a bar complaint, a cyber insurance audit, or a malpractice discovery request, a security assessment is the logical starting point.
Frequently Asked Questions
1. What does ABA Rule 1.6 require from a law firm’s technology?
ABA Model Rule 1.6 requires attorneys to take “reasonable measures” to prevent unauthorized disclosure of or unauthorized access to client information.
In practice, for any firm operating with cloud-based software or networked devices, this means AES-256 encryption at rest and in transit, multi-factor authentication on all access points, role-based access controls that limit who can reach which data, and comprehensive audit logging of all access events.
What qualifies as reasonable is contextual, but the baseline in 2026 is substantive for any firm handling privileged attorney-client communications.2. Does ABA Rule 1.6 require law firms to use cloud hosting?
ABA Rule 1.6 does not mandate cloud hosting specifically. However, ABA Formal Opinion 477R (2017) and ABA Formal Opinion 498 (2021) confirmed that cloud computing is permissible under the rule, provided the firm takes steps to verify that the provider meets the rule’s confidentiality requirements.
Those steps include confirming the use of strong encryption, enforced access controls, audit logging, and clear contractual obligations around data security and breach notification from the vendor.3. What happens if a law firm violates ABA Rule 1.6 through a data breach?
A technology-related violation of ABA Rule 1.6 can result in bar discipline ranging from public censure to license suspension, and in severe cases, disbarment. Beyond bar consequences, affected clients may bring civil malpractice claims where they can demonstrate concrete harm from the unauthorized disclosure.
Courts have also imposed sanctions on firms that failed to protect privileged communications or discovery materials. The severity of consequences typically depends on whether the firm had implemented reasonable safeguards before the breach occurred, not just what happened during it.4. What is the difference between ABA Rule 1.6 and IRS Publication 4557?
ABA Model Rule 1.6 governs attorney-client confidentiality and is enforced through state bar associations under professional conduct rules. IRS Publication 4557 is federal regulatory guidance for tax preparers, enforced by the IRS, and specifically requires a Written Information Security Plan (WISP).
A law firm that does not provide tax preparation services is not subject to IRS Publication 4557. Both frameworks require similar technical safeguards, but they apply to different professional categories and are enforced by entirely different authorities.5. How is technology support for law firms different from general managed IT services?
Technology support built for law firms must address both the operational requirements of legal practice and the specific confidentiality obligations under ABA Rule 1.6. That means direct familiarity with legal practice management platforms like Clio, MyCase, PracticePanther, Smokeball, and CosmoLex, and a working understanding of the compliance framework those applications operate within.
A general managed services provider without legal vertical experience may deliver technically sound infrastructure that still leaves compliance gaps specific to attorney-client confidentiality requirements, gaps that become visible only when a bar inquiry or insurance audit begins.