Adam Dekker, CFP®, EA, CDFA®, runs a fully digital financial planning and tax services firm with three people, no physical office, and a client base that trusts him with some of the most sensitive data a professional can hold.
For years, his entire security posture was himself, a search bar, and a hope. “Our solution before was basically me doing everything in-house,” he says. “We had kind of cobbled together a variety of solutions from off-the-shelf antivirus and a cloud-based data server and just Googling, ‘Hey, how do I set these best practices for laptop security?'”
He did the best he could. The problem was that he knew it was not enough.
The anxiety that came with that knowledge was relentless. “I was constantly living in fear of a security breach or something like that,” Adam says. “That would have been very bad for our business. And I didn’t have a solution.”
His mental disaster plan, if something truly went wrong, was to buy a new computer, absorb serious downtime, restore whatever he could, and never really find out what caused the breach in the first place. For a firm where, in his own words, “we can’t work if our data isn’t accurate, properly secured, and our uptime is 100%,” that was not a plan. It was a prayer.
The moment things shifted was not a breach. It was a requirement. As an enrolled agent and NAEA (National Association of Enrolled Agents) member, Adam became aware that the IRS WISP mandate was not something he could keep deferring. “A big part of what initially drew me to Verito was the requirement of the Written Information Security Policy,” he says. “I was like, ‘Well, I don’t know how to write that on my own.’ I realized I could just download something boilerplate, but everybody’s like, ‘Yeah, that doesn’t really protect you because it’s not customized.'”
Through the NAEA, he found Verito. And what he discovered was not just a WISP solution. It was exactly what he had not known he was looking for. “I didn’t know it, but that was what I was looking for: kind of an all-in-one solution where I could offload the security management of our company to somebody else who actually knew what they were doing.”
Adam’s story is not an edge case. It is the most common path into this conversation that tax and accounting professionals take.
Most firms that currently operate without a compliant written information security plan are not being reckless. They are being human: busy, resource-constrained, and confident that what they have assembled is probably close enough. It is not. Under IRS Publication 4557 and the FTC Safeguards Rule, building and maintaining a proper WISP for CPA firms of every size is a federal legal requirement, not a recommendation, not a stretch goal, and not something that applies only to practices with a dedicated IT department.
Every U.S. tax preparer who receives, processes, or transmits taxpayer information is covered. All of them. Full stop.
Table of Contents Show
Quick Answer: WISP for CPA Firms
A Written Information Security Plan (WISP) is a formal, written document that defines how a tax or accounting firm protects client data from unauthorized access, breaches, and cyberattacks. It is a federal legal requirement, not a recommendation, for every U.S. tax preparer who receives, processes, or transmits taxpayer information.
The requirement is established by IRS Publication 4557 and enforced through the FTC Safeguards Rule (16 C.F.R. Part 314), which classifies tax preparers as financial institutions under the Gramm-Leach-Bliley Act. It applies to every firm regardless of size: solo practitioners, enrolled agents, virtual tax firms, and multi-partner CPA practices equally.
A compliant WISP must document a named security coordinator, a written risk assessment, administrative safeguards, technical safeguards, physical safeguards, an incident response plan, employee training records, and an annual review log. One properly structured WISP satisfies both IRS and FTC requirements simultaneously.
PTIN renewal requires a signed attestation that a data security plan is in place. Filing that attestation without a compliant WISP in place creates direct legal liability.
Key Takeaways
- A Written Information Security Plan (WISP) is a federally required, documented security program that every CPA firm must maintain under IRS Publication 4557 and the FTC Safeguards Rule, with no size exemptions.
- The requirement covers solo practitioners, enrolled agents, virtual tax preparation firms, and any tax professional holding an EFIN or using professional tax software, equally and without exception.
- A compliant WISP must document administrative, technical, and physical safeguards, along with a written risk assessment, incident response procedures, vendor oversight, and a dated annual review process.
- PTIN renewal now includes a mandatory attestation that a data security plan is in place. Submitting that attestation without an actual, compliant WISP creates direct legal liability.
- Adam Dekker, CFP®, EA, CDFA®, spent years running DIY security at his three-person virtual tax firm, living in his own words in “constant fear” of a breach. He found Verito through the NAEA specifically because of the IRS WISP requirement, and offloaded his entire security program to a team that knew what they were doing.
- Verito’s VeritShield WISP service delivers an audit-ready, IRS Publication 5708-aligned written information security plan customized to your firm’s actual environment in under five business days, with less than one hour of work required from your team.
Is your firm’s IT infrastructure built to stay compliant long-term? Future-proof your firm with Verito’s range of Managed IT and Cloud Hosting services.
What Is a Written Information Security Plan?
A Written Information Security Plan, commonly referred to as a WISP, is a formal, written document that defines exactly how your firm protects sensitive client information from unauthorized access, data breaches, and cyberattacks.
It describes who is responsible for data security at your firm, what tools and policies are in use, and the specific procedures your team follows when handling, storing, or transmitting client tax data. It is not a general cybersecurity awareness document or a vendor brochure about data safety. It is your firm’s legally defensible compliance record.
For tax and accounting firms, a WISP is not simply an IT document. It is a compliance instrument built around the specific regulatory frameworks that govern how firms like yours are required to protect client data.
This distinction matters because a generic cybersecurity policy does not satisfy the IRS or FTC. What they want to see is a documented program aligned to their specific requirements, one that covers your actual software environment, your actual staff, and your actual data storage locations, including QuickBooks files, Drake return databases, Lacerte client records, and years of archived tax documents.
Why the IRS Defines a WISP as Non-Optional
IRS Publication 4557, officially titled “Safeguarding Taxpayer Data: A Guide for Your Business,” is the IRS directive establishing that every tax professional must implement and maintain a data security plan.
The IRS developed Publication 4557 in collaboration with Security Summit partners, a coalition of the IRS, state tax agencies, and tax industry software companies, specifically to translate complex cybersecurity obligations into practical, actionable requirements for small and mid-sized practices.
Alongside Publication 4557, the IRS published Publication 5708, which provides the actual implementation framework: a step-by-step guide and sample WISP template that practitioners can use to build a compliant plan.
Together, these two publications define both the requirement and the method. When a tax preparer renews their PTIN each year, they must attest that their firm has a data security plan in place. That plan is the WISP. Providing a false attestation creates direct legal exposure. Operating without any plan at all is a violation of federal requirements before any audit or breach ever occurs.
What’s New in 2026
2026 Compliance Update: FTC Breach Notification Now Required
As of the updated FTC Safeguards Rule, tax professionals must now report any security incident affecting 500 or more individuals to the Federal Trade Commission as soon as possible, and no later than 30 days from the date of discovery. The same incident must also be reported to an IRS Stakeholder Liaison and the relevant state tax authority.
This requirement applies regardless of firm size. If your incident response plan was written before August 2024, it needs to be updated to include these notification timelines and the specific contacts for FTC reporting.
What Happens to a CPA Firm Without a WISP
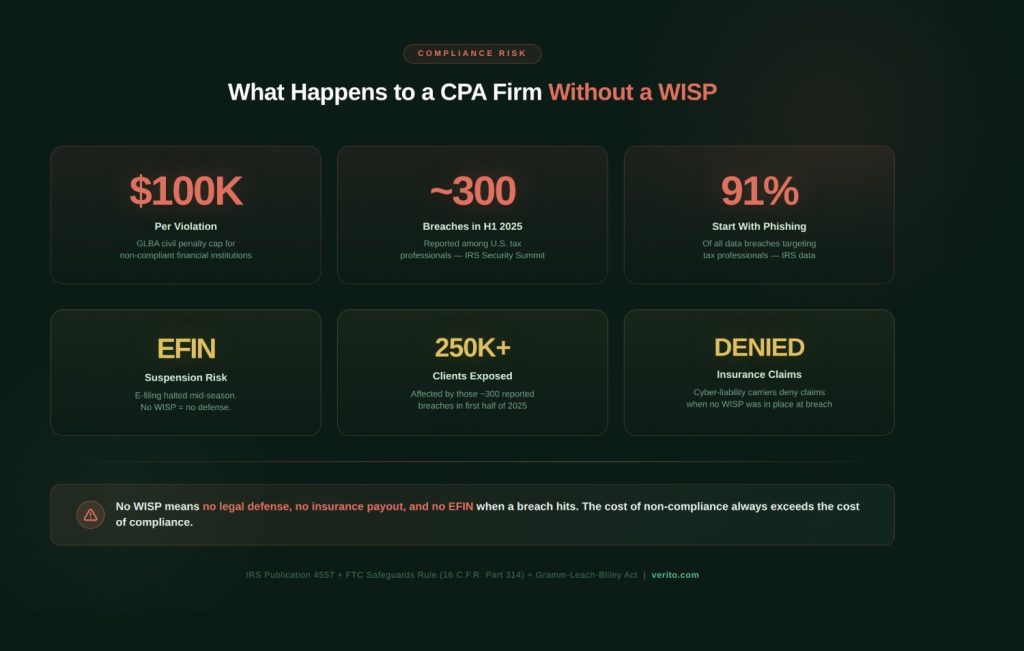
The consequences of operating without a written information security plan extend well beyond a single regulatory fine. Under the Gramm-Leach-Bliley Act (GLBA), the federal statute that underlies the FTC Safeguards Rule, civil penalties for non-compliant financial institutions, a category that explicitly includes tax preparers, can reach $100,000 per violation. Personal liability for firm partners is also on the table.
According to the IRS Security Summit, nearly 300 data breaches affecting as many as 250,000 clients were reported among tax professionals in the first half of 2025 alone, a figure the IRS has published as part of its ongoing Security Summit reporting at IRS.gov.
Cybercriminals target CPA firms specifically because a single compromised account can yield hundreds of Social Security numbers, bank routing details, and Employer Identification Numbers in one attack.
A firm that suffers a breach without a documented WISP faces not just the breach costs themselves but also insurance claim denials, EFIN (Electronic Filing Identification Number) suspension, and reputational damage that takes years to undo. According to the IRS, an estimated 91 percent of all data breaches targeting tax professionals begin with a spear phishing email, which means the threat is not theoretical.
It is active, it is common, and it specifically targets firms like yours.
Who Must Have a WISP: Every Firm, No Exceptions
The scope of the WISP requirement is one of the most consistently misunderstood aspects of data security compliance in the tax profession.
Many practitioners assume the obligation applies only to firms above a certain size or revenue threshold. It does not. The regulatory framework is broad by design, and the IRS has been explicit in its guidance that the size of the firm is irrelevant to the compliance obligation.
The FTC Safeguards Rule (16 C.F.R. Part 314) classifies tax preparers as financial institutions under the GLBA because they are significantly engaged in providing financial services. That classification places every tax preparer inside the same regulatory category as a mortgage lender or a bank, at least where customer data protection obligations are concerned.
This is why the WISP requirement cannot be dismissed as something that applies to “bigger firms with IT departments.”
The IRS Publication 4557 Scope
IRS Publication 4557 applies to any business that receives, processes, or transmits taxpayer information in connection with preparing or filing federal tax returns.
The covered entities include CPA firms of every size, enrolled agents (EAs), bookkeepers who handle tax return preparation or processing, virtual and fully remote tax preparation firms, and any professional holding an EFIN or using professional tax software such as Drake, Lacerte, ProSeries, UltraTax CS, CCH ProSystem fx, or CCH Axcess.
The IRS and Security Summit partners have repeatedly emphasized that criminals do not discriminate by firm size. A three-person CPA practice holds the same volume of sensitive Social Security numbers, bank account details, and employer identification data that a larger firm does, which makes it just as valuable a target.
The FTC Safeguards Rule and the Legal Framework Behind the IRS Mandate
IRS Publication 4557 directs practitioners to the FTC Safeguards Rule for the specific implementation requirements behind the mandate.
The Safeguards Rule was substantially updated in 2021, with revised requirements taking effect in 2023. The updated version is far more prescriptive than its predecessor. Where the original rule required firms to have “appropriate safeguards,” the revised rule mandates specific actions:
- Designating a qualified individual to oversee the security program.
- Conducting a written risk assessment, implementing multi-factor authentication (MFA) on all systems containing client data.
- Encrypting data both at rest and in transit.
- Performing a vulnerability assessment at least every six months.
One properly structured WISP can satisfy both IRS Publication 4557 and the FTC Safeguards Rule at the same time. The key is coverage. When your plan documents the required elements of both frameworks, you do not need two separate compliance documents.
State-Level WISP Requirements: What Multi-state Firms Need to Know
The federal framework: IRS Publication 4557 and the FTC Safeguards Rule, establishes the national minimum. Several states have added their own requirements on top of it, and CPA firms with clients in those states must meet whichever standard is more stringent.
1. Massachusetts
Massachusetts is the most prescriptive. Under 201 CMR 17.00, any business that handles personal information belonging to Massachusetts residents must maintain a comprehensive written information security program.
The requirements overlap heavily with the FTC Safeguards Rule but add specific mandates around encryption of laptops and portable devices and annual employee training documentation. Massachusetts is widely considered the gold standard for state-level data security law.
2. California
California does not mandate a WISP by name, but the California Consumer Privacy Act (CCPA) and its amendment, the CPRA, require reasonable security procedures for any firm handling California resident data. In practice, maintaining a compliant WISP is the most defensible demonstration of those “reasonable procedures”, and CPA firms handling California clients should treat it as effectively required.
3. Texas
Texas under the Identity Theft Enforcement and Protection Act requires businesses that maintain sensitive personal information to implement reasonable security procedures and practices, including written policies that align closely with WISP standards.
For any firm with clients across multiple states, compliance means meeting the most demanding applicable standard. In most cases, a WISP that fully satisfies IRS Publication 5708 and the FTC Safeguards Rule will meet or exceed state requirements but the Massachusetts encryption and training documentation requirements deserve specific attention during annual review.
What a WISP Must Contain: 8 Required Components

IRS Publication 5708 is specific about what a compliant written information security plan must include. A WISP that covers general intentions without detailing the components below will not satisfy an IRS inquiry, an insurance carrier’s underwriting review, or an FTC audit. The following eight elements are not optional additions to a strong compliance posture. They are the baseline.
1. Designated Security Coordinator (Qualified Individual)
Your WISP must name a specific person, with their title and responsibilities documented in writing, who is accountable for implementing and maintaining the security program.
In a small firm, this is typically the managing partner. In firms using a managed IT provider, the provider’s certified security lead can serve this role, provided the designation is formally documented. The IRS and FTC both require that this individual be named, not just implied.
2. Written Risk Assessment
A formal, documented evaluation of every location where client data exists: workstations, cloud servers, mobile devices, email systems, printed files, and any third-party platforms.
The assessment must identify threats, rate their likelihood and potential impact, and document the current controls in place. It must be updated annually and after any material change to your business or technology environment.
3. Administrative Safeguards
Policies governing how your team handles data day-to-day. This includes your employee onboarding and offboarding procedures, access authorization and revocation policies, remote work protocols, and the rules governing how you evaluate and contract with third-party vendors who handle client information.
If a vendor touches your client data and your WISP does not address that relationship, you have a documented compliance gap.
4. Technical Safeguards
The specific technology controls protecting your systems. The FTC Safeguards Rule names MFA, encryption of data at rest and in transit, secure remote access protocols, a defined patch management schedule, and activity monitoring as required technical controls.
Documenting that you “use security software” is not sufficient. Your WISP must name the specific tools, their configurations, and your review schedules.
5. Physical Safeguards
Controls that protect physical hardware and printed records. This covers locked filing cabinets, clean desk policies, physical access controls to spaces where client data is stored, and documented procedures for the secure disposal of hard drives, USB drives, and printed tax documents.
Physical safeguards are the most frequently skipped section in DIY WISPs, and they are an active area of IRS scrutiny.
6. Incident Response Plan
A documented, step-by-step procedure defining what your firm does when a breach occurs. This must include who is responsible for containment, how and when affected clients and regulators are notified (the IRS, the FTC, and many state attorneys general have specific notification timelines), and how your firm conducts its post-incident review.
Writing the plan is required. Testing it and retaining records of that test is what makes it defensible.
7. Employee Training Program
Documented, recurring security training for every staff member with access to client data. Training must cover phishing recognition, password hygiene, safe use of email and file-sharing tools, physical security practices, and how to report suspicious activity.
Completion must be logged, with dates and attendance records retained. The IRS has explicitly flagged ongoing training as a required element, not a nice-to-have.
8. Annual Review and Update Procedure
The WISP is a living document, not a filing cabinet artifact. It must be reviewed at least once per year and updated whenever a significant change occurs: new software, new employees, new office locations, a change in cloud hosting provider, or a security incident.
Every review must be dated and logged. A WISP with a single creation date and no revision history will not pass a 2026 audit.
The 2026 WISP Compliance Checklist for CPA Firms
This checklist maps directly to IRS Publication 5708 and FTC Safeguards Rule requirements. A firm that can answer “yes” to every item below has a defensible, audit-ready security program. Any “no” is a documented compliance gap that needs to be addressed before an incident forces the issue.
2026 WISP Compliance Checklist
| Compliance Control | Required By |
|---|---|
| Qualified Individual designated and named in writing | Both |
| Written risk assessment completed, dated, and on file | Both |
| MFA enabled on all systems containing client data | FTC Safeguards Rule |
| Client data encrypted at rest and in transit | Both |
| Access controls implemented: role-based, least-privilege | Both |
| Annual employee security training documented with records | Both |
| Incident response plan written, tested, and dated | Both |
| Vendor and service provider oversight clauses in contracts | Both |
| Vulnerability assessment completed every 6 months | FTC Safeguards Rule |
| WISP reviewed and updated annually (revision log present) | Both |
| Physical safeguards documented (disposal, locks, facility access) | Both |
| PTIN renewal attestation of data security plan in place | IRS Publication 4557 |
How to Build a Written Data Security Plan for Your Accounting Firm
Building a WISP from scratch is a substantial undertaking. IRS Publication 5708 itself acknowledges this, and most practitioners without compliance or IT experience underestimate the time investment. Before starting, it is worth being realistic: a compliant, customized WISP typically takes 20 or more hours to build properly without expert guidance. That does not mean it is impossible. It means it requires a real commitment of time, not an afternoon.
For firms evaluating template options, it is crucial to understand the different types of WISP templates for accounting firms and what makes each appropriate for different firm types and sizes.
Step 1: Inventory Your Data Environment
Document every location where client tax data exists, including cloud servers, local workstations, mobile devices, email systems, printed files, client portals, and third-party platforms your staff uses. You cannot protect data you have not located.
Step 2: Conduct and Document a Risk Assessment
For each data location identified in Step 1, assess the likelihood and potential impact of a security threat. Identify what controls currently exist and where the gaps are between your current posture and what the FTC Safeguards Rule requires. This assessment must be written and dated.
Step 3: Designate Your Qualified Individual (QI)
Assign a named person to own the WISP. Write their name, title, specific responsibilities, and contact information directly into the plan. For firms using an external IT provider, ensure the provider can formally serve this role and that the designation is documented in your WISP.
Step 4: Draft and Document Your Safeguards in Specific Terms
Write out your administrative, technical, and physical controls with specificity. Naming the tool, the configuration, and the review schedule is what separates a compliant WISP from a generic template. "We use MFA" will not satisfy an auditor. "We use [specific tool], enabled on all cloud-hosted software and email accounts, reviewed quarterly by [name]" will.
Step 5: Write Your Incident Response Plan
Define your breach response procedure step-by-step. Assign roles, establish notification timelines, list the regulatory contacts you are required to notify (IRS, FTC, state attorney general), and document your escalation path. Then test the plan, even informally, and retain a record of the test.
Step 6: Schedule Your Annual Review
Set a recurring calendar event for WISP review before each tax filing season begins. Log every update with the date and a brief description of what changed and why. A documented revision history is one of the most important signals of an active, maintained compliance program.
The Mistakes That Invalidate a WISP Even When One Exists
The financial services sector experienced an average data breach cost of $6.08 million in 2024, according to IBM's 2024 Cost of a Data Breach Report. For a small CPA firm, a fraction of that figure would be catastrophic.
The painful reality is that many of the firms that suffer the worst consequences from a breach actually had a written information security plan on file. The problem was that the plan had not been maintained. Auditors and insurance carriers are not asking whether a WISP exists. They are asking whether it is current, specific, and implemented.
1. Treating the WISP as a One-time Document
The FTC Safeguards Rule requires annual review and updates after any significant business change. A WISP created in 2022 with no revision history will not satisfy a 2026 audit. The IRS expects a living document, not a filing cabinet artifact.
2. Using a Generic Template Without Customization
Free templates, including the IRS's own Publication 5708 sample, provide a structural starting point. They do not describe your specific firm's data environment, your actual tools, or your actual staff roles. An auditor or insurer looking at a template with placeholder text that was never replaced will not treat it as a compliant plan.
3. Failing to Name the Qualified Individual
The IRS and FTC both require a specific, named person to be accountable for the security program. "Our IT department" or "our cloud provider" is not sufficient without a named individual explicitly designated in the document.
4. Missing Vendor Oversight Documentation
Your written data security plan must address every third-party service that handles client data: cloud hosting providers, payroll platforms, document management tools, and client portals. If your SOC 2 Type II-certified hosting provider is not named in your WISP and their data protection obligations are not documented, you have a compliance gap regardless of how strong their infrastructure actually is.
5. No Incident Response Testing
Writing a breach response plan satisfies one requirement. Testing it and retaining a record of the test satisfies another. Auditors and insurance carriers are increasingly asking for evidence of tested response procedures, not just a written plan.
Free WISP Template vs. Expert-Built WISP: An Honest Comparison
There are two realistic paths for a CPA firm that needs a compliant written information security plan.
The first is a free template, including the IRS Publication 5708 sample or Verito's free downloadable version. The second is a purpose-built, expert-led WISP delivered by compliance specialists. Both paths are legitimate. The question is whether the outcome of the first path actually satisfies the requirement.
A free template is better than nothing today, particularly for a solo practitioner with no existing plan who needs to attest at PTIN renewal. But for any firm with staff, client volume, or cyber-liability insurance requirements, the audit exposure created by an incomplete, generic, or unmaintained WISP can far outweigh the cost of doing it right. Understanding the true cost of IRS WISP compliance is an important step before choosing between these paths.
| Factor | Free WISP Template | VeritShield Expert-led WISP |
|---|---|---|
| Time to complete | 20+ hours (DIY) | Under 5 business days |
| Customized to your firm | No | Yes |
| IRS Publication 5708 alignment | Framework only | Verified and documented |
| FTC Safeguards Rule compliance | Partial | Full |
| Risk assessment included | No | Yes |
| Annual review and update support | No | Yes |
| Audit-ready on day one | No | Yes |
| One-time cost | Free | $499 |
How VeritShield WISP Helps CPA Firms Get Audit-Ready
Verito works exclusively with tax and accounting firms. That single fact changes what a WISP delivered by the VeritShield team looks like compared to what a generic compliance consultant produces.
A VeritShield engagement is not a template with your firm's name dropped in. It is a purpose-built compliance document that reflects your actual software stack, whether that is QuickBooks Desktop, Drake, Lacerte, UltraTax CS, or ProSeries. It reflects your actual headcount, your actual remote work setup, and your actual data storage environment.
The VeritShield WISP service delivers an audit-ready, IRS-aligned written information security plan in under five business days, with less than one hour of work required from your team. The plan is aligned to both IRS Publication 5708 and the FTC Safeguards Rule, and includes a written risk assessment, gap analysis specific to your firm, annual review support, and hands-on help establishing and documenting your Qualified Individual.
When your cyber-liability insurer or an IRS auditor asks for your WISP, you have a document that was built to answer exactly those questions.
The practical difference this makes in day-to-day firm operations is captured in how Adam Dekker describes life after switching to Verito's managed approach. The constant background anxiety of running DIY security, the hours spent Googling best practices, the dread of a breach he had no real plan for, all of it is gone.
"It takes a lot of mental load off of my plate as a business owner to know that somebody is looking out for my computers, making sure that we can continue to do our job," he says.
Security now runs quietly in the background, compliant and maintained, without interfering with the work his firm is actually there to do. "I know it's there and I know it's working, but it's not obtrusive, getting in the way of what we're trying to do." That is what a properly implemented written information security program actually looks like in practice: not a burden, but a baseline.
Free Template vs. Expert-Built WISP
WISP Resources and Further Reading for Tax and Accounting Professionals
WISP compliance intersects with IRS Publication 4557 mechanics, the FTC Safeguards Rule, template selection, cost planning, and the day-to-day realities of running a tax practice. Depending on where you are in the process, some of these areas will need more attention than others. The following guides go deeper on each one:
- What Is a WISP? :The right starting point if you are building your understanding from the ground up. Covers the core definition, why the requirement exists, and what it means for firms at every size.
- Written Information Security Plan for Accounting Firms : A detailed walkthrough of how to build a WISP that satisfies both the IRS and FTC frameworks within a single document, without duplicating effort.
- WISP Templates for Accounting Firms : A side-by-side comparison of the available template options and what makes each one appropriate for different firm types, sizes, and compliance situations.
- IRS Publication 4557 WISP Compliance Guide : A section-by-section breakdown of IRS Publication 4557 and how its requirements translate directly into firm operations, written specifically for small and mid-sized practices.
- The True Cost of IRS WISP Compliance : An honest accounting of what building and maintaining a compliant WISP actually costs in time, tools, and ongoing effort, useful reading before deciding between DIY and expert-led options.
Frequently Asked Questions About WISP for CPA Firms
1. Does a solo CPA practitioner need a WISP?
Yes. The IRS Publication 4557 requirement applies to every tax preparer who handles client data, regardless of firm size. A solo practitioner working from a home office is covered under both IRS Publication 4557 and the FTC Safeguards Rule. The IRS has explicitly stated that even one-person practices that operate entirely virtually must maintain a written data security plan covering all devices and locations used for client work.
2. What is the difference between IRS Publication 4557 and IRS Publication 5708?
IRS Publication 4557 establishes the requirement for a WISP and outlines the data protection principles all tax preparers must follow. IRS Publication 5708 is the implementation companion: it provides a sample WISP template and step-by-step guidance for building a compliant plan. Think of Publication 4557 as the "why and what" and Publication 5708 as the "how."
3. Can one WISP satisfy both IRS and FTC Safeguards Rule requirements simultaneously?
Yes, when properly structured. A single written information security plan that addresses risk assessment, administrative safeguards, technical safeguards, physical safeguards, incident response procedures, vendor oversight, and an annual review process will satisfy both IRS Publication 4557 and the FTC Safeguards Rule at the same time. Dual compliance through a single document is specifically encouraged by IRS guidance.
4. How often does a WISP need to be updated?
At minimum, a WISP must be reviewed and updated once per year. It must also be updated whenever a material change occurs in your firm: hiring remote employees, switching accounting software, changing cloud hosting providers, adding a new office location, or experiencing any security incident. Every update must be logged with the date of the review and a description of what changed.
5. What happens if a CPA firm fails a PTIN renewal because no WISP is documented?
PTIN renewal now includes an attestation that the preparer's firm has a data security plan in place. Submitting a false attestation creates direct legal liability. Operating without a documented security plan exposes the firm to IRS sanctions that can include EFIN suspension, which effectively halts the ability to e-file returns during tax season. The reputational and financial consequences of an EFIN suspension during peak season are severe.
6. What is a Qualified Individual under the FTC Safeguards Rule?
A Qualified Individual is the named person within or contracted by your firm who is responsible for designing, implementing, and overseeing the information security program. For small firms, this is typically the managing partner or the firm's IT provider, provided the designation is formally documented in the WISP itself. The FTC requires that this individual report on the security program at least annually.
7. Does a WISP need to cover remote employees and home offices?
Yes. Any location or device used to access, process, or transmit client tax data must be covered by the written information security plan. Remote work environments introduce risks around unsecured home networks, personal device use, and physical document handling that the WISP must explicitly address. The IRS has been direct on this point: remote and hybrid work setups do not reduce compliance obligations.
8. What is the penalty for not having a WISP as a tax preparer?
There is no single fixed penalty, but the exposure is meaningful across multiple dimensions. The FTC can pursue civil enforcement actions under the Gramm-Leach-Bliley Act for failure to maintain required safeguards. Cyber-liability insurance carriers can deny claims if a breach occurs and no compliant WISP was in place at the time. The IRS can take action against a preparer's credentials, including EFIN and PTIN suspension. State attorneys general in many states have independent authority to impose penalties for data security failures affecting residents of their state.
9. Is a free IRS WISP template actually sufficient for compliance?
A free template provides a legitimate structural starting point, but it must be fully customized to your firm's specific data environment, tools, workflows, and staff to be compliant. A template document with unfilled placeholder text, or with controls described in generic terms rather than firm-specific ones, will not satisfy an IRS inquiry or an insurance carrier's underwriting audit. Customization is what creates compliance.
10. How long does it take to build a WISP for an accounting firm?
Building a proper written information security plan from scratch, without compliance expertise, typically takes 20 or more hours. This estimate comes directly from the DIY assessment of Verito's WISP specialists, who regularly review self-built plans submitted by firms seeking an upgrade. Expert-led services like VeritShield reduce the timeline to under five business days, with the firm investing less than one hour of their own time in the process.
The Bottom Line on Written Information Security Plan Compliance for CPA Firms
Compliance does not have to feel like a second job. When a WISP is built correctly, it becomes a stable foundation that your firm updates once a year rather than scrambles to reconstruct under pressure.
Verito has helped accounting firms of every size, from solo enrolled agents to 50-person CPA practices, build and maintain the kind of written security programs that hold up under IRS scrutiny, pass insurance underwriting, and protect clients when it matters most. To get an audit-ready WISP built for your firm without the 20-hour DIY process, review what VeritShield includes.
And to understand the broader infrastructure decisions that support long-term compliance, start with how you can future-proof your firm's IT and compliance infrastructure.