Accounting firms are now squarely in the crosshairs of cybercriminals.
Smaller practices that used to fly under the radar are getting hit with the same tactics aimed at large financial institutions, but without the same budget or in-house security team to fall back on.
According to the FBI’s 2023 Internet Crime Report, professional services firms, including tax preparers and accounting practices, ranked among the top targeted sectors for ransomware and business email compromise, with average losses per incident well above those seen in retail or manufacturing.
At the same time, regulators have stopped treating data security as just a “best effort” exercise. The FTC Safeguards Rule explicitly requires tax preparers and many financial professionals to implement and maintain written security programs to protect customer information, while IRS Publication 4557 reminds preparers that protecting taxpayer data is a legal obligation. Cyber insurance questionnaires have also become far more detailed, asking about MFA, endpoint protection, backups, and incident response in ways that quickly expose weak IT environments.
For many small and mid-sized CPA firms, the weak point is not effort or intent. It is the technology foundation.
A single aging server in the back room, a patchwork of laptops bought at different times, free antivirus, and one overworked local IT contact is not enough in 2026. That kind of setup might limp along in the off-season, but it is fragile when staff are working nights and weekends in March and April and cannot afford downtime or security scares.
Modern IT support for accounting firms is no longer just “someone to call when a printer breaks.” It is a combination of managed IT services, cloud hosting, cybersecurity, and compliance support that is built around how CPA firms actually work: seasonal peaks, strict deadlines, remote staff, multiple tax and accounting applications, and sensitive financial data that must stay available and protected.
The stakes are real. When Julie Crowder’s previous hosting provider suffered a ransomware attack, her firm’s data was compromised during one of the worst possible windows: active client work. Verito recovered her data and restored operations within hours. “There was one name that kept coming up in every conversation: Verito,” she said afterward. That kind of recovery is only possible when backup architecture, incident response, and a 24/7 support team are already in place, not assembled in a panic after an attack begins.
The purpose of this article is to break down what that support should look like, what it typically costs, and how to evaluate whether providers, including specialized partners like Verito, are actually equipped to protect your firm.

Table of Contents Show
Key Takeaways
- IT support for accounting firms in 2026 means a completely managed environment: secure cloud or data center hosting for tax and accounting software, managed workstations and laptops, layered cybersecurity, backups, and proactive monitoring.
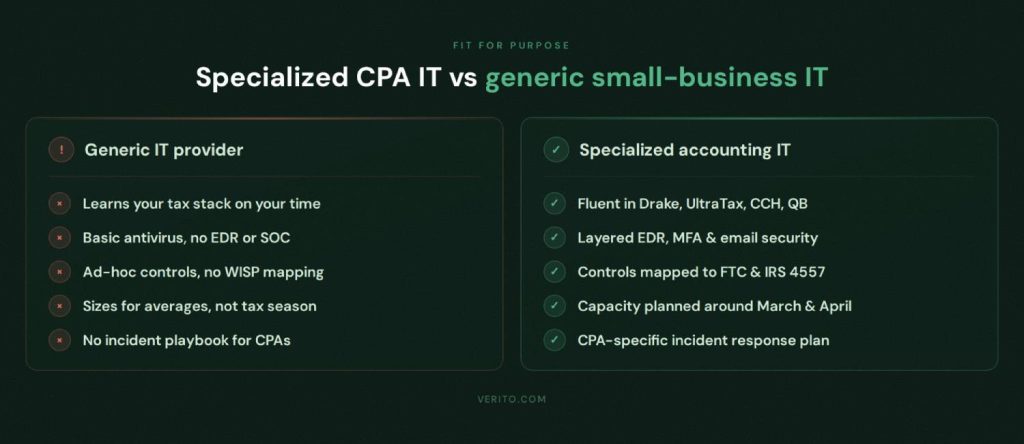
- Generic small business IT providers often struggle with tax season performance, complex accounting software stacks, and regulatory requirements such as the FTC Safeguards Rule and IRS Publication 4557, which is why firms increasingly look for specialist accounting IT partners.
- A modern stack for CPA firms usually includes 24/7 helpdesk support, endpoint detection and response, MFA, advanced email security, secure remote access, structured backup and disaster recovery, user training, and regular security reporting.
- Cloud hosting tailored to accounting workloads lets staff access applications like QuickBooks, Drake, UltraTax, or CCH Axcess from anywhere with consistent performance, while keeping client data in SOC 2 audited data centers rather than on a single office server.
- Compliance is now part of day-to-day IT. A Written Information Security Plan, documented controls, logs, and evidence of testing are necessary both for regulators and for cyber insurance renewals, so your IT provider needs to help build and maintain that documentation.
- Pricing is typically flat fee and per user, with a defined bundle that covers helpdesk, security tools, monitoring, and backups, plus separate project work for migrations and major changes. Hourly “only when something breaks” models are risky for firms that cannot afford surprises in March or October.
- The safest option for most small and mid-sized firms is a specialized provider that understands CPA workflows, tax and accounting software, and regulatory requirements, and can combine cloud hosting, managed IT, and compliance support into a single, predictable service.
What is IT Support for Accounting and CPA Firms in 2026
IT support for accounting and CPA firms in 2026 is best understood as an ongoing service that keeps your entire technology environment secure, available, and compliant with regulations that apply to firms handling financial and taxpayer data.
It covers the systems your staff touch every day, the infrastructure running behind the scenes, and the security controls regulators and cyber insurers now expect to see in place. For most firms, that means a managed IT relationship plus cloud hosting.
Because accounting firms are a regulated, high-value target sector, the bar is higher than for a typical small business. You are not just trying to keep email and file access running. You are protecting Social Security numbers, bank details, payroll records, and historical tax returns. You are also expected to follow the FTC Safeguards Rule, IRS Publication 4557, and in many cases state privacy laws and professional standards. In that context, IT support is the service layer that makes sure your hardware, software, networks, and people operate inside a defensible security and compliance framework every day, including during the busiest points of the tax season.
Modern IT support for CPA firms blends several disciplines that used to be handled separately.
Traditional helpdesk functions are merged with endpoint management, cybersecurity operations, backup and recovery, vendor coordination for tax and accounting applications, and support for compliance documentation efforts like your Written Information Security Plan (WISP).
Done properly, it gives partners one accountable party for the health, security, and readiness of the firm’s technology, whether staff are in the office, at a client site, or working remotely.
Beyond Helpdesk: A Complete IT Stack for CPAs
In many firms, “IT support” still means calling a technician when a workstation crashes or when a tax application refuses to open.
That kind of reactive, ticket-only approach is not sufficient in 2026. A complete IT stack for CPAs starts with reliable helpdesk support, but it extends into proactive monitoring, security, and planning that directly reduce risk and downtime.
At the front line, your staff should have access to a knowledgeable service desk that understands tax and accounting workflows, not just general Windows issues. That includes support for line-of-business applications such as QuickBooks Desktop, Lacerte, ProSeries, Drake, UltraTax, CCH Axcess, and similar tools that often have their own quirks around updates, database performance, and network connectivity. When the helpdesk knows these platforms, tickets get resolved faster and less time is wasted bouncing between vendors.
Behind that, a managed IT provider for accounting firms should be handling the lifecycle of every device and server that touches client data. That includes secure provisioning of new laptops and desktops, standard images for consistent configuration, centralized patching, hardening baselines, antivirus and endpoint detection and response, and controlled removal or wiping of devices when staff leave. These activities are not isolated tasks. They form the foundation that security frameworks and regulatory expectations are built on.
Finally, a complete IT stack for CPAs includes structured backup and disaster recovery, network and connectivity design that can tolerate outages and remote work, and an escalation path to senior engineers and security specialists when there is a serious issue. If your current solution stops at “submit a ticket and hope for the best,” or depends on a single individual’s availability, it falls short of what most firms realistically need in 2026.
Key Components Your Firm Should Expect
When you look at IT support offerings marketed to accounting and CPA firms, the terminology may differ, but the underlying components should look similar. At a minimum, a credible provider in 2026 should deliver:
- A responsive helpdesk service that is available across extended hours and during peak tax deadlines, with clear response and resolution targets and staff who are familiar with common tax and accounting applications.
- Centralized management of desktops, laptops, and other endpoints, including secure configuration, patching, disk encryption where appropriate, and monitoring for hardware or software issues before they lead to outages.
- Secure networking for both office locations and remote users, including properly configured firewalls, segmented networks where needed, protected Wi-Fi, and secure remote access through VPN or “zero trust”-style access controls.
- A layered cybersecurity stack suitable for financial and professional services, combining endpoint detection and response, strong authentication such as MFA, advanced email security with phishing and spam filtering, and web protection to prevent risky browsing from turning into a breach.
- Structured compliance support, including assistance with implementing controls required by the FTC Safeguards Rule and IRS Publication 4557, as well as help creating and maintaining a Written Information Security Plan, security policies, and basic evidence for audits or insurance renewals.
- Cloud hosting or data center services tuned for accounting applications, so that tax software, practice management tools, and accounting systems run from secure, monitored infrastructure instead of a single office server that becomes a single point of failure.
- Regular, tested backups covering servers, hosted environments, and critical workstations where appropriate, with defined recovery point and recovery time objectives that reflect the reality of tax season workloads.
- Continuous monitoring and alerting for infrastructure, services, and security events, so that emerging problems are dealt with proactively.
- Support for user training and awareness, especially in areas like phishing recognition, safe remote work habits, and password or authentication hygiene, which continue to be common sources of security incidents.
- Periodic reporting and strategic input so partners can see trends in ticket volumes, common issues, security events, and capacity constraints, and can adjust budgets and plans accordingly.
If a prospective provider only offers subsets of these capabilities, or expects your partners to manage compliance and security planning alone, they are offering limited technical support.
Why Accounting Firms Need Specialized IT Support, Not Generic Small Business IT
For a typical small business, an IT provider that can set up email, manage a few devices, and fix connectivity issues may be enough.
For a CPA firm, that standard is too low. You are operating in a regulated environment, handling highly sensitive financial and taxpayer data, and working on immovable deadlines. That combination puts you closer to financial services than to a generic small business from a risk perspective.
Regulators and attackers treat you that way. The professional services sector, which includes accounting and legal firms, consistently ranks among the top targets for data breaches that originate from phishing, credential theft, and remote access compromise. Firms hold rich client data, often operate with lean internal IT staff, and have seasonal pressure that makes people more likely to click something risky when they are under time stress. Generic IT providers may understand Windows and Office, but they usually do not build their services around these specific risk factors.
A specialized IT partner for accounting firms designs everything around your tax and accounting stack, your compliance obligations, and your seasonal patterns. That includes how they size hosting infrastructure, how they tune remote access, how they schedule maintenance, which security tools they select, and how they document controls for audits and insurance renewals. It is not simply about better support. It is about a different understanding of what is at stake if your systems go down or your data is exposed in the middle of March or right before an extended deadline.
The Gaps When You Rely on Generic IT

1. Limited Application Expertise
When an accounting firm uses a generic small business IT provider, the problems usually do not appear immediately. Basic services work. Email flows, workstations are joined to a domain, and there may be a local server that shares files. The issues show up when you look at how the environment behaves under stress.
Tax and accounting software is sensitive to network latency, resource contention, and version mismatches.
Generic providers might treat these as software vendor issues and simply point fingers. A specialized accounting IT provider understands that updates to a tax package right before a filing deadline need to be scheduled and tested carefully, and that database locations, folder permissions, and antivirus exclusions all affect performance.
2. Weak Compliance Alignment
Compliance is another major gap. The FTC Safeguards Rule and IRS Publication 4557 both expect financial institutions and tax preparers to implement and maintain administrative, technical, and physical safeguards for customer information, and to document those safeguards. A generic IT shop that does not regularly work with CPA firms may not map its services clearly to these requirements.
You may get ad-hoc security tools without a coherent Written Information Security Plan, or without logging and reporting that demonstrates the controls are actually in place. When a regulator, client, or cyber insurer asks for proof, the firm is left trying to reconstruct documentation after the fact.
3. Tax Season Performance Blind Spots
Tax season performance often exposes misalignment. Generic providers may schedule maintenance or reboots at times that are convenient for them, not realizing that March evenings and weekends are peak hours for your staff. They may also size servers or cloud infrastructure based on average loads rather than peak season, which leads to slow applications and frustrated staff at the worst possible moment.
A specialized partner focuses on performance specifically during filing deadlines and extension periods, which leads to different design and capacity decisions.
4. Unstructured Incident Handling
In a serious event such as suspected ransomware, credential compromise, or a data leak, a generic IT provider might not have a defined incident response process, let alone one tailored for firms that handle taxpayer data. There may be confusion about who notifies clients, how regulators should be engaged, and what forensic evidence must be preserved.
A specialized accounting IT partner will have playbooks that assume financial data sensitivity and regulatory reporting obligations from the outset, so less time is lost figuring out the basics when minutes matter.
Specialized IT vs. Generic IT: Side-by-side
1. Application Expertise
A specialist is comfortable troubleshooting QuickBooks, tax software, practice management platforms, and document management systems that are standard in firms. They understand the interplay between these systems and the underlying infrastructure.
A generic provider might be learning these applications on your time, which leads to longer tickets, more vendor back-and-forth, and more downtime for preparers and staff.
2. Compliance and Documentation
Specialized providers align their services with frameworks and rules that matter for your firm. That might include implementing multi-factor authentication across remote access and key applications, encrypting data at rest, limiting access on a need-to-know basis, and providing templates and support for your Written Information Security Plan.
They expect that auditors or carriers will ask for specific evidence and build reporting that can be presented in a professional way. Generic providers may not have an answer beyond screen captures or informal notes.
3. Uptime and Performance During Peak Season
An accounting-focused provider makes tax season the reference point for planning. Capacity, scaling, and maintenance windows are chosen with March and April in mind. They actively track and target uptime and performance metrics that reflect those critical windows.
Generic IT providers may have good overall uptime numbers, but if the few outages that do occur land during your busiest weeks, the impact on your firm is far higher than their dashboard suggests.
4. Security Depth
Specialized accounting IT support is more likely to include modern endpoint detection and response, stronger logging and alerting, and a security operations function that looks for indicators of compromise relevant to financial and professional services firms.
Generic providers may still rely on traditional antivirus and basic firewalls, which is not enough for current ransomware and credential theft techniques.
5. Support Quality and Context
Specialized providers can often resolve issues on the first call because they recognize the names and behaviors of your applications. Front-line engineers understand that a tax preparer who cannot open a client file during a deadline has very different urgency than a generic user with a minor email issue. That understanding shows up in how tickets are triaged and escalated.
The Verito CPA IT Readiness Framework: 8 Pillars of Modern IT Support
The following eight pillars form what Verito calls the CPA IT Readiness Framework, a structure built around how accounting firms actually operate, not how generic IT providers prefer to package their services. Each pillar represents a distinct area where a gap creates measurable risk for the firm: lost uptime, regulatory exposure, insurance complications, or breach vulnerability.
Firms evaluating their current IT arrangements, or comparing providers, can use this framework as a practical checklist.
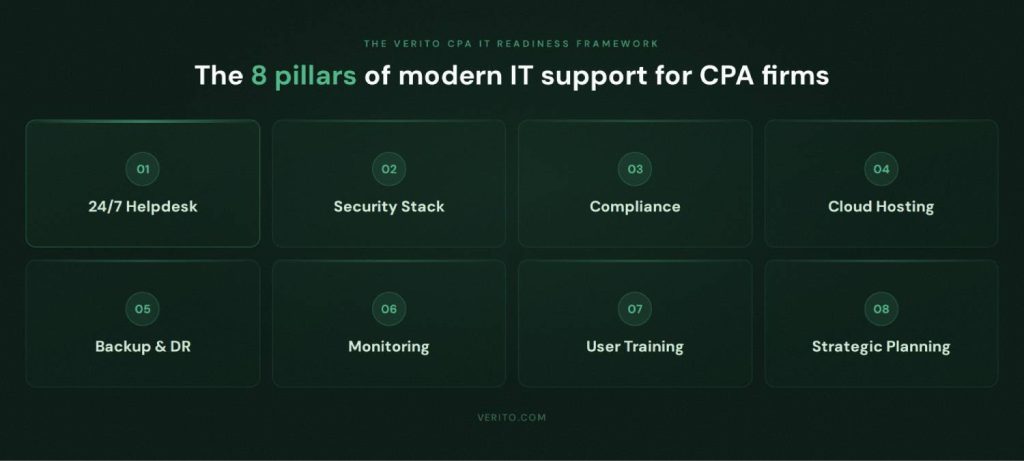
1. 24/7 Helpdesk and Device Support
For a CPA firm, technology support is only useful if it is actually available when staff are working. In practice, that often means early mornings, evenings, weekends, and extended hours during tax season. A help desk that operates on a strict “9 to 5” schedule or that routes everything through a single overworked technician is not aligned with how firms really operate.
A credible IT support model for accounting firms in 2026 includes:
- A centralized service desk reachable by phone, portal, and email.
- Clear response and resolution targets, with higher priority for issues that block billable work.
- Extended or around-the-clock coverage during critical filing periods.
- Engineers who understand common tax and accounting applications.
When frontline support understands tools like QuickBooks Desktop, Lacerte, ProSeries, Drake, UltraTax, CCH Axcess, and practice management systems, most issues can be resolved without long vendor escalations. That shortens ticket times and keeps preparers and staff focused on client files instead of repeating the same problem with multiple people.
Helpdesk coverage should also be tied into device management rather than treated as a separate function. When endpoints are onboarded with standard builds, monitored for hardware errors, and kept patched, many issues can be prevented or at least spotted early. That is very different from a situation where every workstation is unique and only receives attention when it breaks.
From a partner’s perspective, the key indicators to ask for here are:
- Average response time for new tickets
- First contact resolution rate
- Specific experience with accounting and tax software
- Coverage hours during peak tax deadlines
That distinction between accounting-literate and generic support shows up in practice. Ashley M. Moore, a CPA who expanded from solo practice to a multi-staff firm, described the difference when she moved Drake Tax hosting to Verito: “A local IT company doesn’t necessarily specialize in tax and accounting, so there’s kind of a learning curve.”
With Verito, setup required only her Drake serial numbers. Issues that arose during the season were resolved within five minutes. The 45-minute onboarding process versus weeks of back-and-forth with a generic provider is the operational difference between a specialist and a generalist. Read the full story to know more.
If your current IT arrangement cannot provide clear answers for those points, the helpdesk pillar is weaker than it should be for a professional firm handling sensitive data on tight timelines.
2. Security Stack Designed for Ransomware and AI-enhanced Threats
Security is no longer just a box to tick with an antivirus license. For accounting and CPA firms, it is one of the main lines of defense between normal operations and a business stopping incident that risks client trust and regulatory action.
Attackers are increasingly using automation and AI-assisted phishing to target professional services. They know firms store high value financial and taxpayer data and are often under pressure during filing season. Research across small and mid-sized businesses shows that many ransomware incidents now start with a simple phishing email or stolen remote access credentials, then spread rapidly across poorly segmented networks and unprotected endpoints.
For that reason, an IT support partner serving accounting firms in 2026 should provide a layered security stack. That stack should include:
- Endpoint detection and response (EDR) on all firm devices rather than only traditional antivirus.
- Strong multi-factor authentication on remote access, VPNs, email, and key applications.
- Advanced email security with phishing, malware, and spoofing protection, plus policy controls for risky attachments and links.
- Web protection and DNS filtering to block malicious or known bad domains before a browser even loads them.
- Centralized logging and alerting, ideally with a security operations capability that monitors for suspicious activity and responds quickly.
EDR is particularly important for CPA firms. Traditional antivirus focuses on known signatures. Modern EDR tools look for behaviors that suggest ransomware or other malicious activity, even when a specific strain has not yet been seen before. That kind of behavioral detection is what gives you a chance to contain an attack early instead of discovering it only after file shares are encrypted.
Multi-factor authentication is another non-negotiable control at this point. Remote access portals, cloud applications, and even email are common entry points. Without MFA, a single successful phishing email that captures a password can give an attacker direct access to internal systems. With MFA in place, stolen credentials are much harder to exploit.
Email and web filtering matter because many incidents still start with a user clicking a link they should not. No technical control can guarantee that a user will never be tricked, but reducing exposure to obviously malicious messages and domains meaningfully cuts risk. Combined with user awareness training, which is covered later in the training pillar, it creates a much stronger human security layer.
The security stack should also be designed with compliance in mind. Controls like encryption, access logging, MFA, and regular patching are not just good practice, they map directly to expectations in the FTC Safeguards Rule and IRS Publication 4557. If a provider cannot explain how their security tools align with those obligations or provide basic reporting for audits and cyber insurance renewals, their offering is not yet at the level most firms need.
Finally, incident handling is part of the security pillar. A firm should know, in advance, what happens if suspicious activity is detected. That includes how incidents are triaged, who gets notified, how systems are isolated if needed, and how evidence is preserved. A stack of tools without a clear response process is not enough.
3. Compliance By Design: FTC Safeguards Rule, IRS Publication 4557, And WISP
For accounting and CPA firms, compliance is not a separate project that happens once a year.
It is the standard your systems are expected to meet every day. The FTC Safeguards Rule treats many tax and accounting firms as financial institutions and requires them to develop, implement, and maintain a comprehensive information security program. IRS Publication 4557 goes further for tax preparers and spells out how taxpayer data must be protected in practice, including the need for a Written Information Security Plan (WISP).
If your IT support model is not explicitly aligned with these requirements, you are carrying unnecessary regulatory and insurance risk. A provider that only focuses on uptime or basic antivirus can leave you in a position where systems mostly work, but you cannot show a regulator or cyber insurance carrier how they are being protected. In 2026, that gap is no longer acceptable for firms that handle Social Security numbers and detailed financial histories.
A compliance-aware IT partner designs controls so they are part of daily operations instead of static documents. That includes hardening workstations, enforcing multi-factor authentication on remote access, encrypting data at rest in servers and cloud environments, logging access, and maintaining regular patching cycles. It also means having a clear inventory of systems that store or process customer information, which is a direct expectation under the FTC Safeguards Rule.
From a practical standpoint, a firm should expect its IT support provider to help with:
- Creating and maintaining a Written Information Security Plan (WISP) that actually reflects how technology is configured in the firm, not a generic template that sits unused.
- Mapping specific technical controls (MFA, encryption, EDR, backup, logging) to FTC Safeguards Rule requirements and IRS Publication 4557 guidance.
- Providing evidence for audits and cyber insurance questionnaires, such as system inventories, backup reports, patching summaries, and access control reviews.
- Establishing clear procedures for onboarding and offboarding staff, adjusting access when roles change, and documenting who has access to what data.
- Running periodic risk assessments, at least annually, and updating the WISP when new software is adopted, offices are added, or significant changes are made to infrastructure.
Verito’s VeritShield WISP and related services are designed specifically around this problem. They combine WISP drafting with implementation support, so controls defined on paper match what is configured on servers, workstations, and cloud environments. Because Verito operates SOC 2 Type II-certified infrastructure with isolated customer environments, many baseline technical safeguards such as encryption and access controls are already in place at the platform layer, which reduces the burden on small firms that do not have internal security teams.
For solo practitioners and small firms, the compliance requirement can feel particularly daunting without an internal IT team. Melendi Morton, who runs a solo tax and strategy consulting practice in Texas, faced exactly this situation when IRS regulations mandated a WISP to protect her PTIN. “Without dedicated IT support, meeting these requirements seemed overwhelming,” she said.
Verito delivered a compliant hosting environment with documented WISP coverage in under three days. Morton was able to meet IRS Publication 4557 requirements, protect her ability to file returns, and continue serving clients, without becoming an IT expert. “When you have something that’s running and working for you, if nothing’s happening, that’s a good thing.” Read the full story to know more.
For partners, the most important question is: if a regulator, major client, or insurance carrier asked today for proof that the firm is following FTC Safeguards Rule requirements and IRS Publication 4557, could you produce it quickly without scrambling? If the answer is no, your IT support arrangement is not yet operating with compliance by design.
4. Cloud Hosting Optimized for Accounting Applications
For many firms, the single biggest technical risk is still a physical server sitting in an office closet. That server often runs tax applications, accounting systems, file shares, and sometimes even domain services. It may be several hardware generations old, backed up inconsistently, and dependent on a single local IT person for maintenance. When that device fails or is encrypted by ransomware during busy season, the entire firm can grind to a halt.
Cloud hosting for tax and accounting software is the most direct way to remove that single point of failure while giving staff more flexibility. Instead of accessing QuickBooks, Drake, UltraTax, CCH Axcess, Lacerte, or other tools from a local server, users connect to those applications in a managed data center environment that is built to be redundant, monitored, and secure. Done correctly, this is not about moving everything to a public cloud in a generic way. It is about running your applications on infrastructure designed specifically for accounting workloads.
A credible hosting platform for CPA firms in 2026 should provide:
- Dedicated private servers rather than noisy, oversubscribed shared environments, so performance remains consistent even when multiple staff work on large tax files at the same time.
- SOC 2 Type II certified data centers, with strong physical security, network segmentation, and audited controls around access and monitoring.
- Encrypted storage for client data, with backups stored separately and regularly tested for recovery.
- Low latency access for remote work and hybrid teams in accounting firms, so staff can log in from home, client sites, or additional offices without noticeable slowdowns.
- Ability to scale CPU and memory during tax season when usage spikes several times above off-season levels, then scale back to control costs.
- Integration with your firm’s authentication, including multi-factor authentication and least privilege access, so that only the right staff can access specific applications and data.
Verito’s VeritSpace platform is an example of SOC 2 Type II hosting that is tuned specifically for accounting and tax software. It provides dedicated private servers, avoids noisy neighbor problems, and is built to handle 3 to 5 times usage spikes during filing season while maintaining performance and 100 percent uptime. For firms, the outcome is simple: staff can run QuickBooks, Drake, UltraTax, CCH Axcess, and other applications in the cloud without changing core workflows, while significantly reducing the risk associated with an aging, in-house server.
The failure mode this hosting model is designed to prevent is not theoretical. Anna Stevens, a 40-year CPA with a small Florida practice, experienced multiple hard drive failures and data restoration events over a decade of managing her own in-office server. “I can remember several times where we had a hard drive that failed and had to have data restored,” she said.
After moving to Verito’s cloud infrastructure, the hardware risk was eliminated entirely. The migration was so smooth she describes barely remembering it happened. Now her firm operates with zero server maintenance and support response times under five minutes for any issues that arise. (Full story)
Good hosting, however, is only part of the picture. The desktops and laptops that connect to those hosted environments still need to be managed and secured. That is why many firms look for an integrated model where cloud hosting and managed IT services sit under one umbrella, rather than splitting responsibilities between multiple vendors. When a single partner is responsible for both the hosted environment and the endpoints, there is less confusion about ownership and more consistent enforcement of security controls.
For firms evaluating this approach, it is worth looking at providers who treat hosting and ongoing support as part of a broader framework of managed IT services for accounting firms. That kind of relationship usually covers hosting, endpoint security, backups, compliance support, and an IT helpdesk for CPAs in one structure, so partners are not left coordinating between several vendors when issues arise.
5. Backup, Disaster Recovery, and Cyber Insurance Readiness
When partners think about security, they often picture firewalls and antivirus. In reality, the control that determines whether a serious incident becomes a business-ending event is often backup and recovery. If your firm can restore systems quickly to a known-good state, ransomware, hardware failure, or accidental deletion becomes an operational problem instead of an existential one.
For accounting and CPA firms, good backups are not just about having a copy of files somewhere. They are about designing and testing a full recovery strategy with clear objectives that match the firm’s risk tolerance and tax season realities.
A sound backup and disaster recovery approach for a CPA firm in 2026 should include:
- Multiple backup copies of critical systems and data, stored both onsite (or in primary data centers) and offsite in logically separate locations, with encryption in transit and at rest.
- Defined recovery point objectives (RPO) that specify how much data the firm is willing to lose in a worst case scenario. For many firms in busy periods, that may mean backups throughout the day, not just overnight jobs.
- Defined recovery time objectives (RTO) that set expectations for how long key systems can be down. For tax and accounting applications in March or April, acceptable downtime is often measured in hours, not days.
- Regular restore testing that confirms backups can actually be used to bring systems back online.
The link between backups and cyber insurance is direct. Underwriters now routinely ask detailed questions about backup frequency, separation from production systems, encryption, and proof of testing. A firm that cannot answer those questions clearly may see higher premiums, heavier conditions, or even difficulty renewing coverage. An IT partner that understands this landscape can help shape backup architecture so it meets both operational and insurance expectations.
Backups also have to cover modern hybrid environments. If you run applications in hosted environments and keep some data in on-premises systems or local devices, you need a strategy that accounts for each layer. That might mean image-level backups for servers, file-level backups for specific shares, and policies that ensure critical data on laptops does not live only on the endpoint.
Finally, a disaster recovery plan is more than just technology. It should document who makes decisions in an incident, how communication with staff and clients is handled, what order systems are restored in, and how regulators or agencies are notified if taxpayer data might be involved. Your IT support provider should help define and update this plan, and should be prepared to execute it if an incident occurs.
If your firm’s current backup arrangement boils down to “we think there is a backup running on that device in the closet,” then the backup and recovery pillar is exposed. In 2026, that is a risk both regulators and insurers will eventually surface, usually at the worst possible time.
6. Monitoring, Patch Management, and Performance Tuning
A healthy IT environment does not stay that way by accident.
Systems drift out of date, logs fill up, disks approach capacity, and small glitches compound into outages. For CPA firms that depend on a handful of core applications during very specific windows of the year, that kind of slow degradation is risky. Monitoring, patch management, and performance tuning are the preventive maintenance-side of modern IT support.
Monitoring starts with visibility. Your IT provider should have tools that continuously check the health of servers, hosted environments, workstations, and network devices. That includes watching for high CPU and memory usage, low disk space, failed services, unusual login activity, and connectivity problems. The goal is to spot early warning signs and fix them before they turn into tickets or downtime.
Patch management is the process that keeps operating systems and key software up-to-date with security fixes and stability improvements. For firms in a regulated environment, timely patching is not just best practice, it is a common requirement in security frameworks and in guidance like IRS Publication 4557. The challenge is that updates for tax and accounting applications must be handled carefully to avoid breaking workflows close to filing deadlines.
A mature patch management approach for accounting firms typically involves:
- Regular, scheduled patch cycles for operating systems and standard applications, with maintenance windows that avoid peak working hours during busy season.
- Separate processes for tax and accounting application updates, including testing in a staging environment before production roll out when possible.
- Central reporting that shows patch status across all managed devices and servers, so gaps can be identified and addressed quickly.
- Clear rules for emergency patching when high-severity vulnerabilities are disclosed, balanced against the need to keep production systems stable.
Performance tuning ties directly to staff productivity. If your core applications are consistently slow, staff either spend more time waiting or try to work around systems in ways that can create new risks. For hosted environments, performance tuning might involve adjusting server resources, optimizing storage, reviewing network paths, and ensuring that antivirus or EDR tools are configured to avoid unnecessary overhead on databases and application directories. For on-premises equipment, it may involve upgrading hardware that has reached its limits.
For CPA firms, monitoring and tuning should be anchored around peak tax season use. Your IT support provider should be reviewing metrics from prior seasons, looking at ticket patterns, and adjusting resource allocations well before the next peak period starts. That can include adding capacity for hosted environments, upgrading bandwidth, or rebalancing workloads across servers.
From a partner’s perspective, the questions to ask here include:
- What monitoring tools are in place for servers, networks, and endpoints, and how often are they reviewed?
- How does the provider handle patching for both operating systems and critical applications, and how do they avoid applying untested changes right before deadlines?
- What process do they use to decide whether to scale resources up or down for hosted environments, especially around tax season?
- How often do they review performance data and ticket trends with firm leadership?
When monitoring, patch management, and tuning are handled well, you see fewer surprises, fewer emergency tickets, and a smoother experience during the most important weeks of the year. When they are neglected, you feel it in slow systems, unstable updates, and outages that always seem to land at the worst possible time.
7. User Training and Human Risk Reduction
Even the strongest technical controls can be undermined by a single rushed click. For accounting and CPA firms, that is a real concern, because staff are often working under time pressure, juggling client requests, and dealing with large volumes of email. Attackers know this and deliberately target professional services with convincing phishing campaigns that copy tax software vendors, banks, or even the IRS.
User training and awareness are therefore not optional extras. They are central to a realistic security strategy. A good IT support partner will treat people as part of the security stack and build training, testing, and guidance into their services.
Effective security awareness training for CPA firms usually has several parts.
First, there is foundational education on topics like phishing, password hygiene, safe use of remote access, and handling of sensitive client data. This should be delivered in practical language that reflects the tools staff actually use, such as email systems, tax software, and hosted desktops. It should also be refreshed regularly, not given once and forgotten.
Second, there is simulated phishing. Staff receive test messages designed to mimic real attacks. When someone clicks a link or enters credentials in a simulation, they are redirected to a short learning module. Over time, this helps reduce risky clicks and gives partners real data on how often staff are being fooled and how quickly they are improving.
Third, there is role-specific guidance. Partners and managers might need to focus more on social engineering attempts that target their authority, such as fraudulent wire instructions or fake client messages. Administrative staff might need extra help with document handling and recognizing dangerous attachments. All staff should understand basic procedures for reporting suspicious messages or activity, and should feel safe doing so even if they are unsure.
The IT support provider should also anchor user training in the firm’s policies and WISP. That means training aligns with documented expectations for handling customer information, remote work, device use, and incident reporting. When regulators or auditors ask how staff are trained, the firm can point to specific content and completion records.
For partners, the main indicators to look for are:
- Whether the IT provider offers a structured security awareness program, not just an occasional newsletter.
- Whether simulated phishing is included and reported on in a way that leadership can understand.
- Whether training content is tailored to professional services and accounting, rather than generic small business examples.
- How often training is refreshed and how new hires are onboarded into the program.
Without these elements, the human side of your security posture is largely left to chance, which is risky in a sector where a large share of incidents begin with a staff member being tricked into taking an action that bypasses technical safeguards.
8. Strategic IT Planning and Reporting
The final pillar of modern IT support for accounting firms is often the least visible day-to-day, but it has a significant impact over time. Strategic IT planning and reporting is what keeps your technology aligned with the firm’s growth, service mix, and risk profile, instead of drifting along as a collection of short-term fixes.
In practice, this takes the form of a regular planning function, often called a virtual CIO or vCIO role. The IT provider assigns a senior person who understands both technology and accounting firm operations. That person meets with partners to review current systems, ticket trends, security events, and upcoming changes in the firm. The outcome should be a simple, prioritized roadmap that covers the next one to three years.
For a small or mid-sized CPA firm, that roadmap might include plans to:
- Retire aging servers and move additional applications into secure hosting environments.
- Standardize laptops and desktops on a smaller set of models and configurations to simplify support and security.
- Upgrade network connectivity to support more remote work and additional offices.
- Phase in new security controls such as passwordless authentication or stricter access controls for high risk data.
- Schedule major software upgrades outside of peak tax deadlines, with testing and rollback plans.
Strategic planning should also integrate regulatory changes, vendor roadmaps, and lessons learned from incidents. For example, if a new IRS or FTC guideline affects how taxpayer data must be handled, the vCIO function should translate that into concrete changes in configuration or workflow, rather than leaving partners to interpret legal language on their own.
Reporting is the counterpart to planning. A good IT support provider will not just send raw system metrics. They will present clear summaries that answer business questions, such as:
- Are we seeing fewer critical incidents over time, and why or why not?
- Which parts of our environment generate the most support tickets?
- How many security alerts were raised and how were they resolved?
- Whether backup jobs and restores have been successful, and how long restores took in testing?
- Where patch compliance stands across the fleet and which systems are lagging?
These reports give partners a way to judge whether IT support is improving the firm’s risk posture and productivity. They also help with budgeting. Instead of reacting to sudden large expenses when something fails, the firm can plan for replacements and improvements gradually, based on a clear picture of asset age, support status, and business needs.
Finally, strategic planning and reporting are where your IT support partner demonstrates that they understand your firm as a professional services business. They should be asking about your growth plans, new practice areas, potential mergers, and changes in staffing. That context influences everything from how they design hosted environments to how they structure licenses and security policies.
When this pillar is missing, firms often find themselves in a cycle of urgent fixes, unplanned hardware replacements, and reactive security spending. When it is in place, technology decisions become more predictable, more aligned with partner goals, and less disruptive to day-to-day work.
What the Right IT Support Looks Like for Firms of Different Sizes
Not every CPA firm needs the same IT footprint, but every firm needs a coherent, defensible one. The right model depends on your size, mix of services, and internal capabilities. This section looks at what “good” typically looks like for three common stages: very small practices, growing firms, and established multi-office firms.

1. Solo and Very Small Firms (1–5 People)
Solo CPAs and very small firms usually run a tight operation. A few desktops or laptops, a primary tax application, perhaps QuickBooks Desktop or a similar accounting package, cloud email, and a mix of locally stored and cloud-stored documents. Sometimes there is still a small server in the office, but increasingly these firms rely on hosted or cloud-based applications.
The risks are still significant. A single compromised laptop can expose years of taxpayer data. A local drive failure can compromise client records if there is no reliable backup. Many solo practitioners also have limited time to troubleshoot issues, so every hour lost to IT problems directly cuts into billable work.
What “Right” IT Support Looks Like
For this segment, the goal is to get enterprise-grade protection and stability without unnecessary complexity. In practice, that usually means:
- Moving tax and accounting applications into secure hosting, so there is no single vulnerable server in the office.
- Standardizing on a small set of properly configured laptops or desktops with disk encryption, EDR, and MFA in place.
- Using managed IT services that include patching, monitoring, backup, and a responsive helpdesk for core applications.
- Having a simple but complete WISP and basic documentation so regulatory and insurance questions can be answered without stress.
A bundled model that combines cloud hosting with managed IT support is often the most efficient fit here. Instead of coordinating between separate hosting, local IT, and security vendors, the practitioner has one partner accountable for availability, security, and compliance. That is where offerings like Verito’s combined cloud hosting and managed IT for accounting firms are often a practical option. The firm gets a predictable per user model that covers most of what they need, which is important when cash flow and time are both tightly managed.
Maureen Sittig, president of SoCo Business Solutions, a full-service bookkeeping firm, migrated over 50 QuickBooks Desktop client accounts to Verito’s servers and describes the experience plainly: “QuickBooks ran and still runs smoothly and quickly on the server.” Her team and her clients now have access to 24/7 support, and she notes that Verito proactively communicates any downtime or server issues rather than waiting for clients to report problems.
2. Growing Firms (6–25 Staff)
In the 6 to 25-staff range, many firms hit the limits of informal IT. Shared passwords, ad-hoc file shares, a mix of personal and firm devices, and a single aging server all become harder to manage. New hires come on board more frequently, offices may expand, and partners start feeling the strain of coordinating several technology vendors.
At this stage, the firm is also more visible. Clients are often larger, cyber insurance requirements are stricter, and questions about how client data is protected start appearing in RFPs and due diligence questionnaires.
Without a managed structure, IT issues escalate. Staff experience slow applications, confusing VPN setups, and inconsistent access. Partners hear about problems only when something breaks. No one has a clear map of systems, and the WISP, if it exists, is usually a static document that does not match reality.
What “Right” IT Support Looks Like
For a growing CPA firm, IT support needs to shift from reactive to structured. A solid model at this stage usually includes:
- A full managed IT service for accounting firms, with per user pricing that covers helpdesk, endpoint management, security tools, and backups.
- Hosting or data center services for tax and accounting software with documented uptimes, performance guarantees, and peak season planning.
- A defined onboarding and offboarding process, where new staff receive properly configured devices and access, and departing staff lose access predictably.
- A maintained WISP, mapped to FTC Safeguards Rule and IRS Publication 4557, with at least annual risk assessments and updates.
- Regular reporting and planning sessions so partners understand where bottlenecks and risks are, and can budget for improvements.
This is often where firms get the most benefit from combining VeritSpace hosting with VeritGuard managed IT services or using an all-in-one structure such as VeritComplete. Instead of guessing whether the local server can handle another two tax seasons, the firm migrates core workloads to a SOC 2 Type II hosted environment and has managed IT services to maintain endpoints, networks, and security controls. That combination significantly cuts down on the “IT surprises” that derail tax season.
3. Established And Multi-office Firms (25–50+ People)
Once a firm reaches 25 to 50 staff, complexity rises quickly. There may be multiple offices or a mix of office and fully remote staff across states. The firm might have several lines of service, such as audit, tax, advisory, and client accounting services, each with its own tools and data flows. Some firms in this segment either have or are considering internal IT hires.
At this size, the stakes around security and uptime are higher. A serious incident can affect hundreds or thousands of clients. An extended outage during filing deadlines can write-off a significant share of seasonal revenue. Larger clients may also demand contractually defined security standards and may ask for evidence of compliance with industry frameworks.
Co-managed IT and Advanced Services
The right IT support model for this group often becomes co-managed. Internal IT staff can handle certain day-to-day tasks, business-specific workflows, and local office logistics, while a specialized external provider delivers:
- Hosting and infrastructure management for tax and accounting applications.
- Advanced security services, including EDR, SOC monitoring, and incident response.
- Standardized endpoint management and patching across locations.
- Structured backup and disaster recovery across hosted and remaining on-premises systems.
- Strategic planning, reporting, and compliance support at a level that internal IT alone may not be able to sustain.
In a co-managed arrangement, roles and responsibilities need to be clearly defined. For example, Verito might take ownership of VeritSpace hosted environments, VeritGuard endpoint and security management, and WISP documentation, while in-house IT focuses on user training, local office networks, and coordinating with practice leaders. The key is that there are no grey areas where no one is clearly accountable.
Firms at this size should also be thinking in terms of formal frameworks. That does not mean suddenly adopting a heavy enterprise standard, but it does mean aligning controls and documentation with recognized best practices, so audits, vendor assessments, and insurance renewals become more predictable.
Characteristics of a Healthy Setup at this Stage
An established CPA firm with healthy IT support usually has:
- No single point of failure such as a lone server or a lone technician.
- Standardized device builds and configurations across the firm.
- Hosted or data center environments for high value applications, with documented uptime and performance history.
- A live WISP that staff actually know exists and that matches what systems are doing.
- Regular, structured meetings between partners, internal IT (if present), and the external provider to review performance, security, and upcoming changes.
If any of those pieces are missing, the firm is relying on luck more than it should, given the volume and sensitivity of client data it holds.
How Much Does IT Support for Accounting Firms Cost in 2026
IT support costs depend on firm size, service scope, and whether you are still on break-fix or have moved to a managed services model. That said, there are clear patterns in how CPA firms are billed in 2026 and some realistic budget ranges you can use as a sanity check. The key is to look beyond headline price and examine what you actually get for the package you opt for.
1. Hourly or Break-fix vs. Flat-fee Managed IT
A lot of firms still start with hourly or “as needed” IT. You call someone when a workstation dies, a tax application crashes, or the server is running out of space. You get a bill for the hours and maybe some hardware. On paper, this feels cheaper. In practice, it usually costs more once you factor in downtime, lost billable hours, and the fact that no one is being paid to prevent problems.
With break-fix:
- There is no incentive for your IT contact to reduce tickets. They are paid when things go wrong.
- Proactive work such as monitoring, patching, and documenting your environment is minimal or non-existent.
- Bills arrive at random and often at the worst possible time, like in the middle of March when something fails.
- Security and compliance become afterthoughts because no one is accountable for them unless you explicitly pay for separate projects.
Managed IT flips that model. You pay a predictable monthly fee, usually per user or per device, and in return the provider takes responsibility for a defined set of services. Those services cover helpdesk, monitoring, patching, backups, security tools, and often some level of compliance support. The provider is financially motivated to keep your environment stable and secure because constant problems eat into their margins.
For CPA firms, the risk profile and deadline pressure mean “hourly only” is generally a poor fit once you have more than one or two people. You might still pay hourly for major projects or unusual issues, but the day-to-day running of your systems is better handled under a flat fee managed model. It gives partners predictable costs and gives someone clear responsibility for keeping the firm secure and operational.
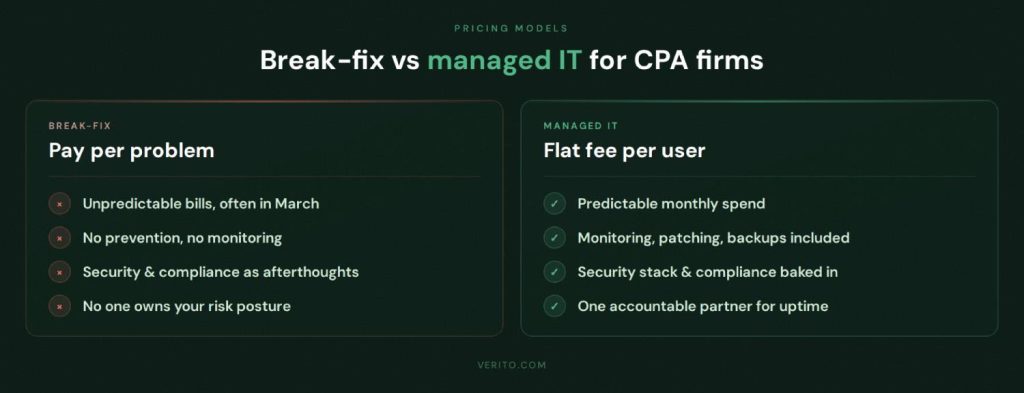
Common Flat Fee Models and What They Include
Most accounting-focused IT providers in 2026 structure pricing around one of two main models.
1. Per user pricing
- A fixed monthly fee per staff member who uses firm systems.
- Usually includes support for all that person’s firm managed devices, access to the helpdesk, security tools, monitoring, and backup for systems under management.
- Works well for firms where staff regularly use multiple devices but you want a simple way to budget per head.
2. Per device pricing
- A fee for each workstation, laptop, server, or sometimes virtual desktop.
- Can make sense in environments with shared devices or part-time staff, but can become messy if people use many devices.
In both cases, the provider will define what is “all inclusive” and what is not. A typical managed IT for accounting firms bundle includes:
- Helpdesk support for office and remote staff during extended hours.
- Endpoint management: standard builds, patching, and monitoring.
- Security stack: EDR, MFA rollout support, email security, web filtering.
- Backup and recovery for servers, hosted environments, and sometimes selected endpoints.
- Basic compliance support: documentation for controls, reports for audits and cyber insurance.
Separate line items that are often charged outside the base fee include:
- One-time onboarding and migration projects, such as moving from on-premises servers to a hosting platform.
- Major infrastructure changes, like adding new offices or redesigning the network.
- Large scale incident response if you come on board after a breach or ransomware event.
For Verito specifically, per user models like VeritGuard and bundled options like VeritComplete are structured to keep that line clear. The monthly price covers ongoing support, hosting for core applications, security, and backup in a defined package, while larger one-time changes are scoped separately. That helps firms avoid surprise invoices while still allowing for growth and upgrades when needed.
When comparing providers, do not just compare the per user fee. Line up what each includes side-by-side. A slightly higher monthly cost that includes a proper security stack, compliance reporting, and tested backups is often cheaper than a low number that leaves you exposed and forces you to buy those elements piecemeal later.
Realistic Budget Ranges for CPA Firms in 2026
Exact numbers will vary by market and provider, but you can use the following as broad guide rails for budgeting IT support for accounting firms in 2026. These ranges assume a modern managed IT relationship with appropriate security controls.

1. Solo and very small firms (1–5 users)
- Total monthly managed IT and basic hosting spend often falls in a band roughly equivalent to what one or two billable hours per user would be worth. For example, a solo practitioner might be in the low to mid hundreds of dollars per month, scaling up as more users and hosted applications are added.
- The goal is to keep the spend small enough to be manageable, but high enough to cover real security and backup, not just ad-hoc support.
2. Growing firms (6–25 users)
- All-in managed IT for accounting firms, including helpdesk, endpoint management, security stack, and backup, commonly lands in a healthy mid three-figure to low four-figure monthly range for the smallest firms in this bracket, scaling up from there based on headcount and complexity.
- Adding SOC 2 type hosting for tax and accounting applications increases costs but removes the need to maintain or replace local servers and reduces the risk of outages in peak season.
3. Established and multi-office firms (25–50+ users)
- Total monthly spend for combined hosting and managed IT often approaches the cost of one to two mid-level internal IT salaries once you include benefits and tools, but delivers a full team, a 24/7 helpdesk, security operations, and compliance support. Many firms in this segment use a hybrid model, with some internal IT plus an external specialist.
However you structure it, a useful benchmark is to ask what percentage of firm revenue is going to core IT and security. Various industry surveys show that small and mid-sized businesses typically spend between 3 and 7 percent of revenue on IT, with more regulated sectors tending toward the higher end. Accounting and CPA firms that handle sensitive data and rely on continuous system availability usually sit closer to that upper range.
For partners, the financial question is less “Can we push this number lower” and more “Does this number match the risk we are carrying and the value of uninterrupted, compliant operations”. If a firm with millions in annual revenue is spending less on IT and security than it writes off in a single missed deadline or small breach, there is probably a misalignment.
When assessing offers, it often helps to look at:
- Cost per user, inclusive of hosting, helpdesk, security, and backup.
- Whether there is a clear project list for larger one-time costs.
- How long-term contracts are structured and whether there are annual increases.
- What reporting you receive demonstrates value, not just activity.
A provider that can explain their pricing in plain terms, map it to specific services, and show how those services reduce measurable risk is generally a safer bet than one that quotes a low headline number with vague inclusions.
How Verito Handles IT Support For Accounting And CPA Firms
Verito is built specifically for tax and accounting professionals.
Its stack covers the full environment firms need in 2026: secure hosting, managed IT, a modern security stack, and practical compliance support. The core services are VeritSpace (hosting), VeritGuard (managed IT and security), VeritComplete (bundled model), and VeritShield WISP (compliance and documentation). Together they map cleanly to the eight pillars in this guide.
Verito runs SOC 2 Type II certified infrastructure with isolated customer environments and encrypted data in transit and at rest. Hosting capacity and support coverage are planned around tax season, not average load. On top of that, Verito operates a 24/7 Pro Help Desk staffed by VeritCertified engineers, trained on servers, accounting software, cybersecurity, and compliance. That combination gives sub one-minute average response times, high first-touch resolution, and support that understands the impact of downtime in March and April.
Across more than 150 verified client reviews, Verito holds a 4.9 rating on G2, with accounting and tax firm owners consistently citing application-specific support knowledge and rapid response times as the differentiating factors, not just general IT competence.

VeritSpace: Hosting for Tax and Accounting Software
VeritSpace is Verito’s dedicated private server platform for tax and accounting applications such as QuickBooks Desktop, Lacerte, Drake Tax, UltraTax, and CCH Axcess. Each firm receives its own private servers to avoid “noisy neighbor” problems and maintain consistent performance when multiple staff work in the system.
Workloads run in SOC 2 Type II data centers with strong physical and logical controls. Storage is encrypted, customer environments are isolated, and multi-factor access is available. Resources can be scaled up before filing deadlines and dialed back after a busy season. The goal is to keep legacy desktop applications and workflows, but run them on a modern, resilient platform instead of a single office server.
VeritGuard: Managed IT and Security for Devices
VeritGuard handles the managed IT and security-side for endpoints and networks. It includes:
- 24/7 remote IT support for staff, including help with common tax and accounting applications.
- Standard builds, patching, and monitoring for desktops, laptops, and other devices.
- Endpoint detection and response, advanced email filtering, and web protection.
- Support for secure remote access with multi-factor authentication.
- Backup management and basic disaster recovery for systems under management.
Because VeritGuard and VeritSpace are delivered by the same team, there is no split between “hosting issues” and “local IT issues”. The same provider sees both ends of the connection and is responsible for fixing problems and keeping controls consistent.
VeritComplete: Hosting and IT in One per User Model
VeritComplete combines VeritSpace and VeritGuard into a single per user model. Firms get hosted desktops and applications, managed endpoints, security tools, backup, monitoring, and access to the 24/7 helpdesk under one predictable monthly fee per user.
For most small and mid-sized CPA firms, this removes the need to coordinate between a hosting vendor, a separate MSP, and a security contractor. There is one contract, one set of service levels, and one accountable partner for uptime, security, and day-to-day support.
VeritShield WISP: WISP and Compliance Support
VeritShield WISP focuses on documentation and regulatory expectations. It helps firms:
- Build or update a Written Information Security Plan that reflects real systems and controls.
- Map technical measures to FTC Safeguards Rule and IRS Publication 4557 requirements.
- Collect evidence such as backup reports, configuration details, and access reviews for audits or cyber insurance.
- Keep the WISP current as applications, hosting, or access methods change.
Because Verito already manages the environment, VeritShield can base the WISP on accurate technical information instead of generic templates.
Support Metrics and Outcomes
Across its client base, Verito targets measurable outcomes: rapid response, high first-touch resolution, and near continuous availability for hosted environments. For accounting firms, the impact is fewer escalations, less back-and-forth between vendors, and more confidence that systems will be available during extended hours in busy season.
Turning IT Support into a Real Advantage for Your Firm
By 2026, IT support for accounting and CPA firms is either a strong foundation or a weak spot.
There is not much middle ground. If you have a single server in a closet, inconsistent backups, basic antivirus, no real WISP, and a reactive local tech, then you are accepting a level of operational, regulatory, and reputational risk that does not match the value of the client data you hold. Cybercriminals, regulators, and insurers are all treating CPA firms like high-value financial targets, and they are not going to ease off.
On the other hand, a modern model that combines specialized cloud hosting for accounting applications, managed IT services for accounting firms, a layered security stack, and live compliance support looks very different. Systems are monitored, patched, and backed up on a schedule. Staff have an accounting-literate helpdesk to call when something breaks. Ransomware and phishing are mitigated by MFA and EDR rather than left to chance. Your WISP is current, tied to actual controls, and can be produced quickly when a client, regulator, or insurer asks.
The practical next step is not to rewrite your entire environment overnight. It is to assess where you are relative to the eight pillars in this guide, then decide whether your current provider can realistically close the gaps. If they cannot, you will need a specialist that treats cloud hosting, managed IT, cybersecurity, and compliance for CPA firms as a combined problem. That is the logic behind platforms like VeritSpace, VeritGuard, and bundled offerings such as VeritComplete, which give firms one accountable partner rather than a loose collection of vendors.
Firms that take this seriously will not just avoid disasters. They will have quieter tax seasons, fewer all-hands scrambles, cleaner audits, and less time wasted worrying about whether tonight’s late shift will be interrupted by a broken VPN or a suspicious email.
If your current setup does not give you that level of confidence, now is the time to fix it, before the next filing deadline exposes the gaps.
FAQ:
1. What does IT support for accounting firms actually include in 2026?
In 2026, IT support for accounting firms is not just someone fixing printers and resetting passwords. It typically includes a 24/7 or extended-hours helpdesk, managed laptops and desktops, secure networking, endpoint detection and response, multifactor authentication, advanced email security, regular patching, and backup with tested recovery.
For regulated firms, it also includes help writing and maintaining a Written Information Security Plan, mapping controls to the FTC Safeguards Rule and IRS Publication 4557, and supplying evidence for cyber insurance and client due diligence. If a provider does not cover most of that, you are buying partial IT support, not a complete solution.2. Do small CPA firms really need managed IT, or is a local tech enough?
A solo practitioner can sometimes get by with ad hoc help, but even very small firms handle enough taxpayer data that a single breach will hurt badly. A one-person tech who only shows up when something breaks usually does not provide ongoing patching, tested backups, or structured security, and those are exactly what regulators and attackers care about.
Managed IT for small CPA firms does not need to be complex, but it does need to be systematic: hardened devices, proper hosting, MFA, backups that are tested, and a simple WISP. Skipping those to save a few hundred dollars a month is a bad trade once you factor in the cost of a serious incident or an insurance denial.3. How often should we update our WISP and security controls?
A WISP is not a one-time document you write and forget. At minimum, you should review and update it annually and any time you make a significant change, such as moving to a new hosting platform, adding an office, adopting a new practice management system, or changing how remote access works.
IRS guidance on safeguarding taxpayer data and AICPA commentary both stress that firms need ongoing risk assessment, not a static plan. If your WISP still describes systems you decommissioned years ago or skips cloud applications you use every day, regulators and insurers will notice, and it will undermine your claims that you are managing risk properly.4. Can we keep some systems on-premises and still be secure and compliant?
Yes, you can run a hybrid environment, but you have to treat on premises systems with the same discipline as hosted ones. That means hardening servers, enforcing MFA on any remote entry points, segmenting networks, patching on a schedule, encrypting data, and backing up to locations that are logically separate from production.
For many smaller firms, the honest answer is that they do not have the time or expertise to do that well, which is why moving tax and accounting software to a SOC 2 audited hosting platform is often safer than keeping an aging office server alive. Hybrid is possible, but doing it properly is not simpler or cheaper than going to a well-run hosted model.5. How does IT support tie into cyber insurance?
Modern cyber insurance applications are detailed and blunt. Carriers want to know if you use MFA on remote access and email, whether you have endpoint detection and response, how often you patch, how backups are configured, and whether you have a current WISP. If you answer optimistically and then suffer an incident, gaps between what you said and what your environment actually looks like can cause coverage fights.
A competent IT support provider should help you answer those questionnaires accurately and put missing controls in place before renewal. If your current provider plays no part in insurance renewals, they are ignoring a risk that directly affects your ability to recover financially from an attack.6. How much should a CPA firm budget for IT and security overall?
There is no single correct number, but you can sanity-check your budget against what others are doing. Various industry surveys, including benchmarking studies from AICPA and Gartner, consistently place technology spending for small and mid-sized professional services firms between 4 and 7 percent of annual revenue, with compliance-heavy sectors trending toward the upper end.
If your firm is spending far less than that on all IT and security combined, yet handles high volumes of sensitive financial and taxpayer data, you are probably under-investing relative to your risk. The point is not to chase a percentage for its own sake, but to be honest about whether your current spend can realistically cover proper hosting, managed IT, security, and compliance support.7. How do we know when it is time to replace our current IT provider?
Common warning signs are not subtle. If you have recurring outages during tax season, vague answers about compliance, no clear WISP support, slow or inconsistent responses, and no structured reporting or planning, your provider is not keeping up with 2026 realities.
Another red flag is if your partners, not your IT provider, are doing all the work answering IT and security questions from clients, regulators, and insurers. At that point you are effectively paying for technical labor but still carrying the strategic and compliance burden on top, which is not sustainable.